System log message destinations, System log facilities and severity levels, 157 system log facilities and severity levels – Juniper Networks J-Series User Manual
Page 179
The JUNOS system logging utility is similar to the UNIX
syslogd
utility. Each system
log message identifies the software process that generated the message and briefly
describes the operation or error that occurred.
Reboot requests are recorded to the system log files, which you can view with the
show log
command. Also, you can view the names of any processes running on your
system with the
show system processes
command.
System Log Message Destinations
You can send system logging information to one or more destinations. The
destinations can be one or more files, one or more remote hosts, the terminals of
one or more users if they are logged in, and the system console.
■
To direct messages to a named file in a local file system, see “Sending System
Log Messages to a File” on page 160.
■
To direct messages to the terminal session of one or more specific users (or all
users) when they are logged into the router, see “Sending System Log Messages
to a User Terminal” on page 161.
■
To direct messages to the router console, see the JUNOS System Log Messages
Reference.
■
To direct messages to a remote machine that is running the UNIX
syslogd
utility,
see the JUNOS System Log Messages Reference.
System Log Facilities and Severity Levels
When specifying the destination for system log messages, you can specify the class
(facility) of messages to log and the minimum severity level (level) of the message
for each location.
Each system log message belongs to a facility, which is a group of messages that are
either generated by the same software process or concern a similar condition or
activity.
Table 81 on page 157 lists the system logging facilities, and Table 82 on page 158 lists
the system logging severity levels. For more information about system log messages,
see the JUNOS System Log Messages Reference.
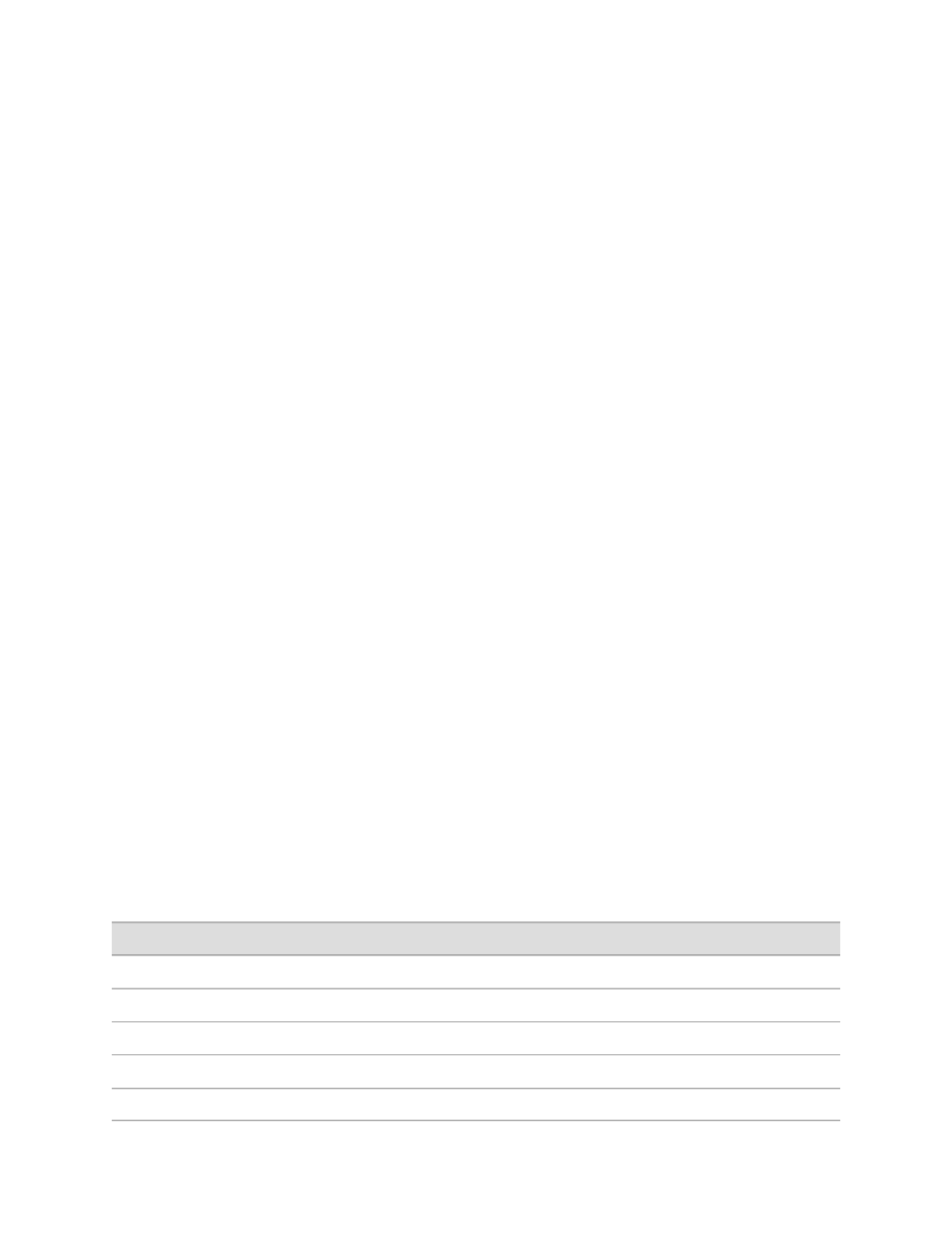
Table 81: System Logging Facilities
Description
Facility
Any facility
any
Any authorization attempt
authorization
Any change to the configuration
change-log
Cron scheduling process
cron
Various system processes
daemon
System Log Messages Overview
■
157
Chapter 8: Monitoring Events and Managing System Log Files
