Setting the agent contact and location information, Limiting tftp servers used through snmp – Dell POWEREDGE M1000E User Manual
Page 734
33-16
Cisco Catalyst Blade Switch 3130 and 3032 for Dell Software Configuration Guide
OL-13270-03
Chapter 33 Configuring SNMP
Configuring SNMP
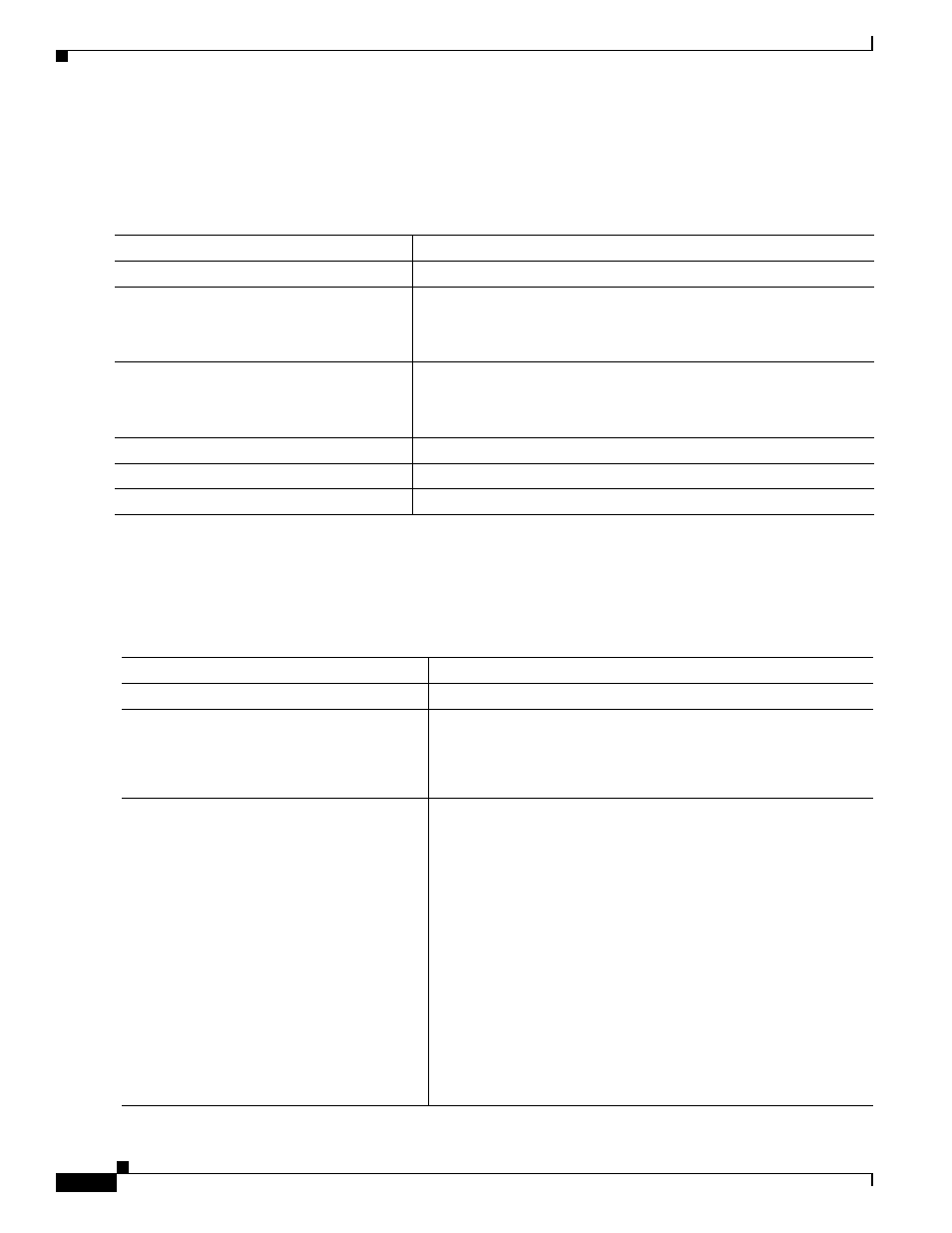
Setting the Agent Contact and Location Information
Beginning in privileged EXEC mode, follow these steps to set the system contact and location of the
SNMP agent so that these descriptions can be accessed through the configuration file:
Limiting TFTP Servers Used Through SNMP
Beginning in privileged EXEC mode, follow these steps to limit the TFTP servers used for saving and
loading configuration files through SNMP to the servers specified in an access list:
Command
Purpose
Step 1
configure terminal
Enter global configuration mode.
Step 2
snmp-server contact text
Set the system contact string.
For example:
snmp-server contact Dial System Operator at beeper 21555
.
Step 3
snmp-server location text
Set the system location string.
For example:
snmp-server location Building 3/Room 222
Step 4
end
Return to privileged EXEC mode.
Step 5
show running-config
Verify your entries.
Step 6
copy running-config startup-config
(Optional) Save your entries in the configuration file.
Command
Purpose
Step 1
configure terminal
Enter global configuration mode.
Step 2
snmp-server tftp-server-list
access-list-number
Limit TFTP servers used for configuration file copies through
SNMP to the servers in the access list.
For access-list-number, enter an IP standard access list numbered
from 1 to 99 and 1300 to 1999.
Step 3
access-list access-list-number {deny |
permit} source [source-wildcard]
Create a standard access list, repeating the command as many times
as necessary.
•
For access-list-number, enter the access list number specified
in Step 2.
•
The deny keyword denies access if the conditions are matched.
The permit keyword permits access if the conditions are
matched.
•
For source, enter the IP address of the TFTP servers that can
access the switch.
•
(Optional) For source-wildcard, enter the wildcard bits, in
dotted decimal notation, to be applied to the source. Place ones
in the bit positions that you want to ignore.
Recall that the access list is always terminated by an implicit deny
statement for everything.
