Rockwell Automation 57C620 AutoMax Programming Executive Version 3.8 User Manual
Page 276
NĆ8
AutoMax Programming Executive Version 3.x
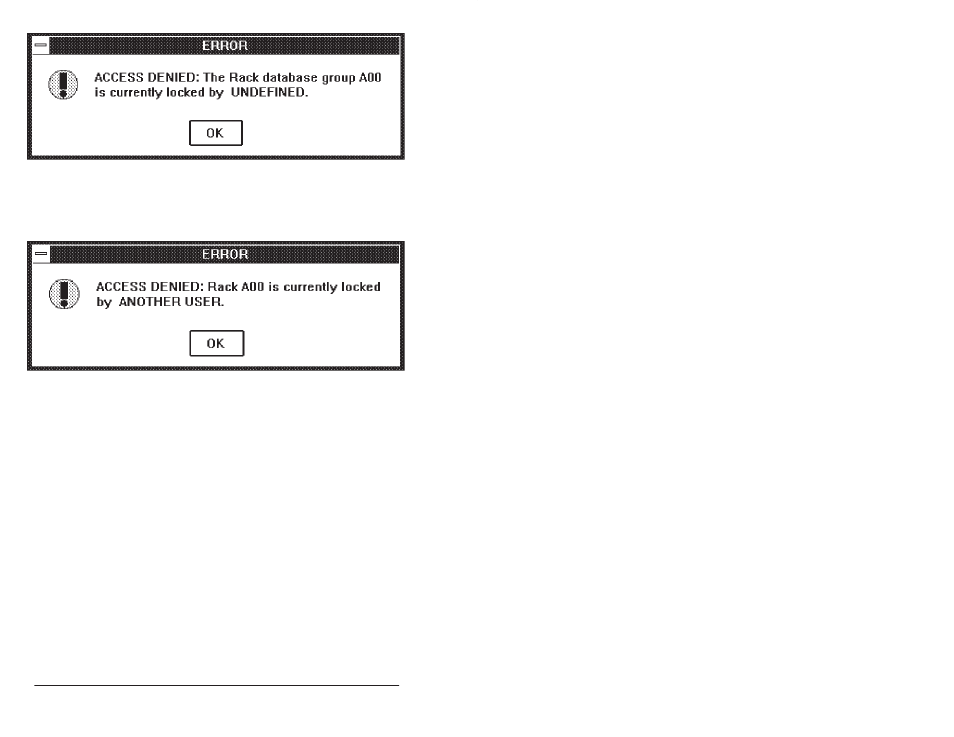
When another user is working at a lower level than the level you are trying to lock
(e.g., editing a task in the rack you are trying to transfer), the AutoMax system
must search for the lock file in order to identify the user who is blocking your lock.
If the offending lock is removed before it is found, it may not be possible to
identify the user. In this case, your lock would still fail and the message would
look something like the following:
Database Lock Time/Date Stamps
In order to create display screens for the user, various AutoMax applications read
information from the databases and store the information in memory. An example
is the rack diagram displayed by the Rack Configurator. In a network
environment, users A and B both might read RACK2 into memory. User B
modifies the information and writes his changes to the database (which releases
the lock) before user A attempts to also modify the rack. User A may then make
modifications based on old information. The result could undo user B's changes
or result in erroneous information. As long as user B was finished making his
changes and had written his changes to the database (released the lock) before
user A attempted to take the lock, the locking scheme alone would not prevent
problems.
For another example, suppose that user A has selected the Rack Configurator
and is viewing a 16Ćslot rack. User B then modifies the rack from a 16Ćslot rack to
a 10Ćslot rack using the Modify command on the Rack menu in the System
Configurator. User A then proceeds to add a module in slot 15, which is perfectly
valid according to the information he has in memory. The result is a module
assigned to a slot which no longer exists in the rack.
To avoid this problem, each lock has a time/date stamp that is updated every time
the lock is issued. Whenever data is read from the database, the time/date stamp
of the lock that protects that database will be saved. When changes are made to
the source copy, the lock covering the files will be taken. If the time and date
match the time/date stamp saved when the data was read, then no one else has
taken this lock and the files have not been changed. If the time or date on the
lock is more recent than the time/date stamp that was saved when the files were
