Vulnerability reports, Creating and generating a report – Fortinet FortiLog-400 User Manual
Page 67
Reports
Vulnerability reports
FortiLog Administration Guide
05-16000-0082-20050115
67
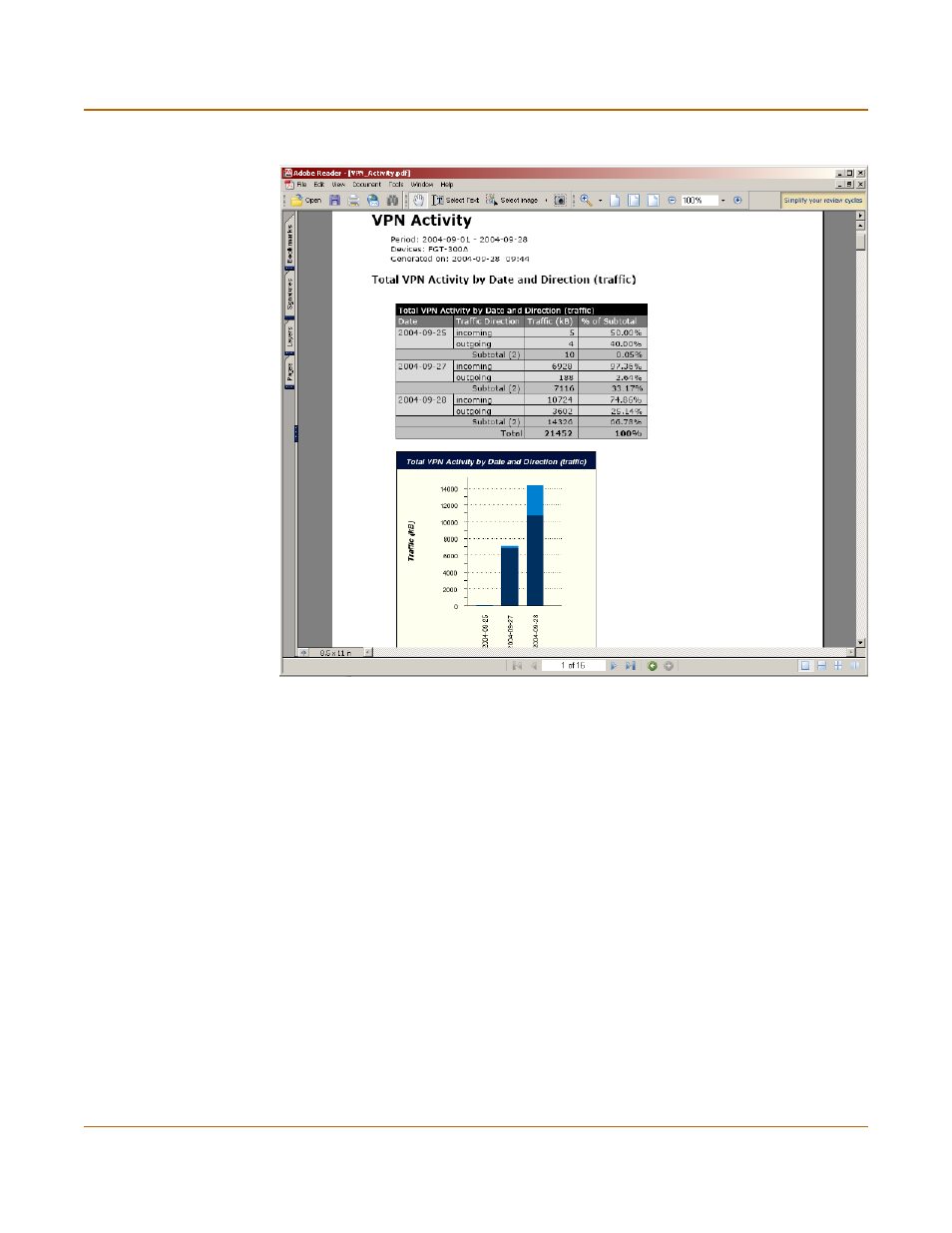
Figure 36: VPN activity report in PDF
Vulnerability reports
Vulnerability reports show any potential weaknesses to attacks that may exist for
selected devices by displaying the available ports on a FortiGate device. Rather than
using the device logs for this report, the FortiLog unit queries for open ports and
where possible and gathers information about the services running. Any known
vulnerabilities that exist for the specific service or version of the service, are included
in the reports.
Creating and generating a report
To generate a vulnerability report, begin by creating and saving a report configuration.
You can use this report configuration for a scheduled report or for generating reports
on demand.
To create a report
1
Go to Reports > Config > Vulnerability.
2
Select New and enter a name for the report.
