Blacklist log auditing, Configuration guide, Operation log auditing – H3C Technologies H3C SecCenter Firewall Manager User Manual
Page 63: N in, Figure 54
57
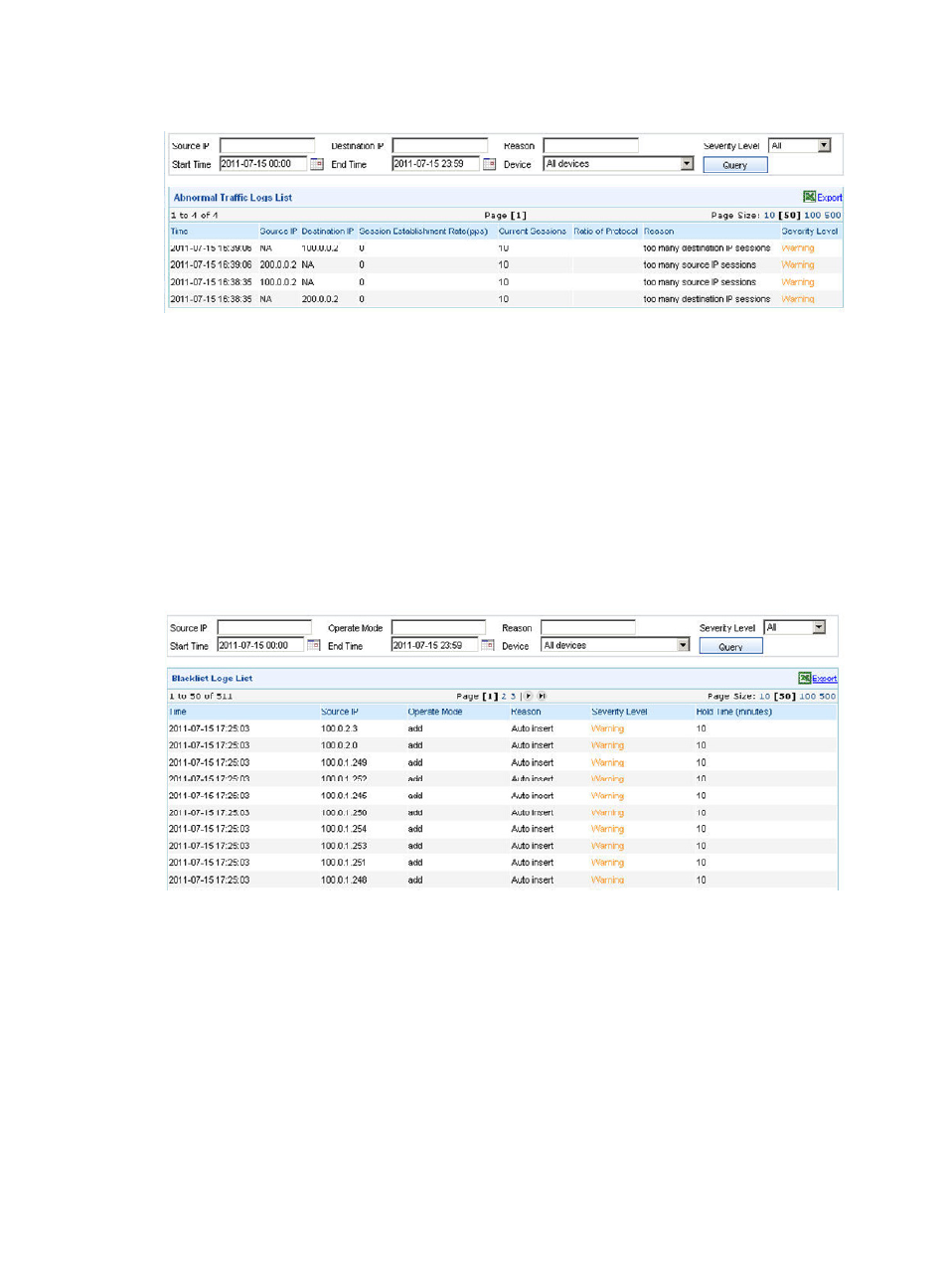
Figure 54 Abnormal traffic log auditing
Blacklist log auditing
Configuration guide
From the navigation tree of the firewall management component, select Blacklist Logs under Event
Auditing to enter the blacklist log auditing page, as shown in
Blacklist filters packets by source IP address. It can effectively filter out packets from a specific IP address.
The blacklist log auditing page lists the blacklist logs of H3C firewalls. Each log records the log time,
source IP address, reason to add the address to the blacklist, as well as the blacklist entry’s severity level,
hold time of the log entry, and operation mode, helping you know the blacklist status of the network.
Figure 55 Blacklist log auditing
Operation log auditing
Configuration guide
From the navigation tree of the firewall management component, select Operation Logs under Event
Auditing to enter the operation log auditing page, as shown in
. This page lists the logs in order
of time, with the most recent log at the top. Each log records the operation’s time, username, IP address
of the PC used to access the system, operation performed, and alarm severity level.
Operation log auditing allows you to query operation logs by username, user IP, operation, severity level,
time, and device group, helping you know the information of login users and track the users’ operations.
