Configuring ssl, Overview, Ssl security services – H3C Technologies H3C S6300 Series Switches User Manual
Page 321: Ssl protocol stack
306
Configuring SSL
Overview
Secure Sockets Layer (SSL) is a cryptographic protocol that provides communication security for
TCP-based application layer protocols such as HTTP. SSL has been widely used in applications such as
e-business and online banking to provide secure data transmission over the Internet.
SSL security services
SSL provides the following security services:
•
Privacy—SSL uses a symmetric encryption algorithm to encrypt data and uses an asymmetric key
algorithm such as RSA to encrypt the key used by the symmetric encryption algorithm. For more
information about RSA, see "
•
Authentication—SSL uses certificate-based digital signatures to authenticate the SSL server and
client. The SSL server and client obtain digital certificates through PKI. For more information about
PKI and digital certificates, see "
."
•
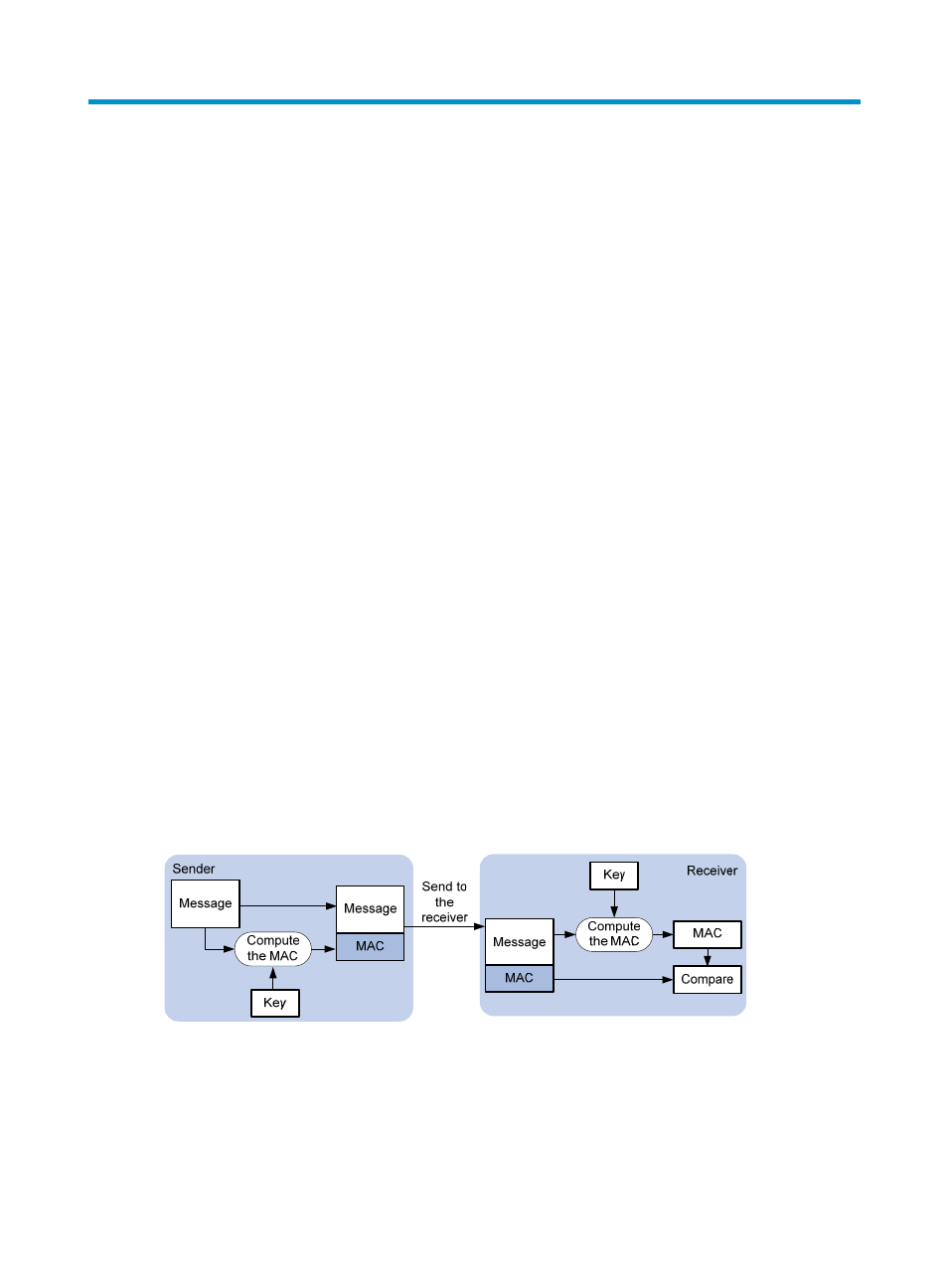
Integrity—SSL uses the message authentication code (MAC) to verify message integrity. It uses a
MAC algorithm and a key to transform a message of any length to a fixed-length message. Any
change to the original message will result in a change to the calculated fixed-length message. As
shown in
, the message integrity verification process is as follows:
a.
The sender uses a MAC algorithm and a key to calculate a MAC value for a message,
appends the MAC value to the message, and sends the message to the receiver.
b.
The receiver uses the same key and MAC algorithm to calculate a MAC value for the received
message, and compares it with the MAC value appended to the message.
c.
If the two MAC values match, the receiver considers the message intact. Otherwise, the
receiver considers the message tampered with and discards the message.
Figure 99 MAC algorithm diagram
SSL protocol stack
SSL includes an SSL record protocol at the lower layer, and an SSL handshake protocol, SSL change
cipher spec protocol, and SSL alert protocol at the upper layer.
