Verifying pki certificates, Verifying certificates with crl checking – H3C Technologies H3C S6300 Series Switches User Manual
Page 208
193
Verifying PKI certificates
Every time a certificate is requested or obtained, or used by an application, it is automatically verified.
If the certificate expires, is not issued by a trusted CA, or is revoked, the certificate is not used.
You can also manually verify a certificate. If it is revoked, the certificate cannot be requested or obtained.
Verifying certificates with CRL checking
CRL checking checks whether a certificate is in the CRL. If it is, the certificate has been revoked and its
home entity is not trusted.
To use CRL checking, a CRL must be obtained from a CRL repository. The device selects the CRL
repository from the following information. When the CRL repository is found, the selection process stops.
The selection order is as follows:
1.
CRL repository specified in the PKI domain.
2.
CRL repository in the certificate to be verified.
3.
CRL repository in the CA certificate, or CRL repository CRL in the upper-level CA certificate if the
CA certificate is the certificate to be verified.
After the previous selection process, if the CRL repository is not found, the device obtains the CRL through
SCEP. To use SCEP to obtain the CRL, the CA certificate and the local certificates must have been
obtained.
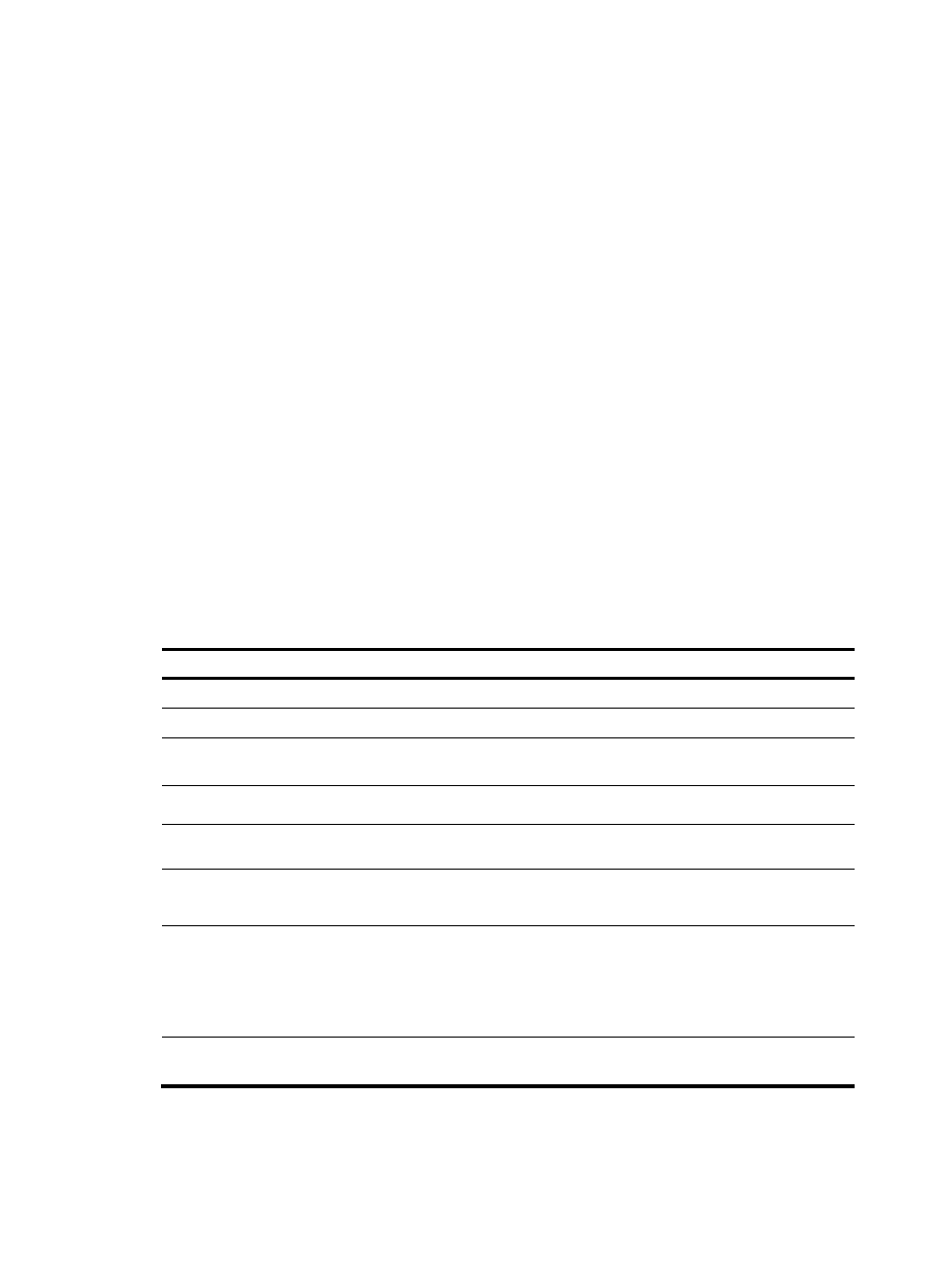
To verify certificates with CRL checking:
Step Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enter PKI domain view.
pki domain domain-name N/A
3.
(Optional.) Specify the URL
of the CRL repository.
crl url url-string
By default, the URL of the CRL
repository is not specified.
4.
Enable CRL checking.
crl check enable
By default, CRL checking is enabled.
5.
Return to system view.
quit
N/A
6.
Obtain the CA certificate.
See "
N/A
7.
(Optional.) Obtain the CRL
and save it locally.
pki retrieve-crl domain
domain-name
The newly obtained CRL overwrites
the old one, if any.
The obtained CRL must be issued by
a CA certificate in the CA certificate
chain in the current domain.
8.
Verify the validity of the
certificates.
pki validate-certificate domain
domain-name { ca | local }
N/A
