Certificate revocation list, Ca policy, Pki architecture – H3C Technologies H3C S6300 Series Switches User Manual
Page 199
184
Certificate revocation list
A certificate revocation list (CRL) is a list of revoked certificates, and is created and signed by a given
CA.
A certificate must be revoked when, for example, the username changes, the private key is compromised,
or the user is no longer certified by the CA. The CA periodically publishes a CRL that contains the serial
numbers of all revoked certificates. CRLs provide an effective way for verifying the validity of certificates.
CA policy
A CA policy is a set of criteria that a CA follows in processing certificate requests, issuing and revoking
certificates, and publishing CRLs. Usually, a CA advertises its policy in a certification practice statement
(CPS). You can obtain a CA policy through out-of-band means such as phone, disk, and email. Make
sure you understand the CA policy before you select a trusted CA for certificate request because different
CAs might use different policies.
PKI architecture
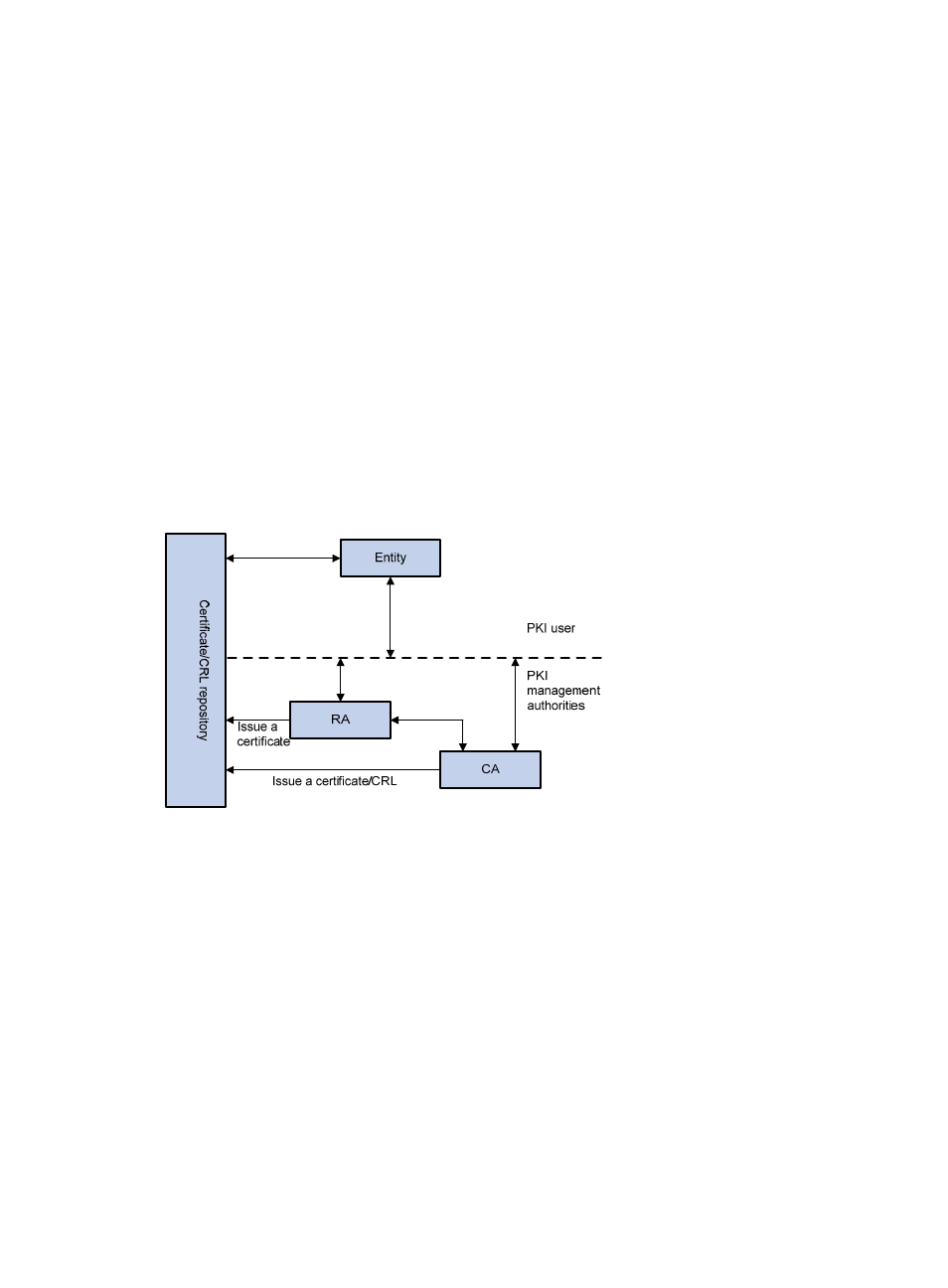
A PKI system consists of PKI entities, CAs, RAs and a certificate/CRL repository, as shown in
Figure 69 PKI architecture
•
PKI entity—A PKI entity is an end user or host using PKI certificates. The PKI entity can be an
operator, an organization, a device like a router or a switch, or a process running on a computer.
The SCEP is a protocol that used by the PKI entity to communicate with the CA and RA.
•
CA—A CA is a trusted authority that issues and manages digital certificates. A CA issues
certificates, defines the certificate validity periods, and revokes certificates by publishing CRLs.
•
RA—In a PKI system with complex CA hierarchical structures, RAs, which are trusted by CAs,
manage registration requests to reduce the burden on CAs. An RA accepts certificate requests,
verifies user identity, and determines whether to ask the CA to issue certificates. RAs are not
allowed to issue certificates.
A CA and its trusted RAs should be on different devices to avoid direct interaction between the CA
and external devices for higher security of the private key of the CA.
•
Repository—A certificate/CRL repository, also known as a distribution point, stores certificates and
CRLs, and distributes these certificates and CRLs to PKI entities. It also provides the query function.
A PKI repository can be a directory server using Lightweight Directory Access Protocol (LDAP) or
HTTP protocol, and LDAP is commonly used.
