Comtrol DeviceMaster LT User Manual
Page 46
46 - DeviceMaster LT Security
DeviceMaster LT User Guide: 2000586
Rev. B
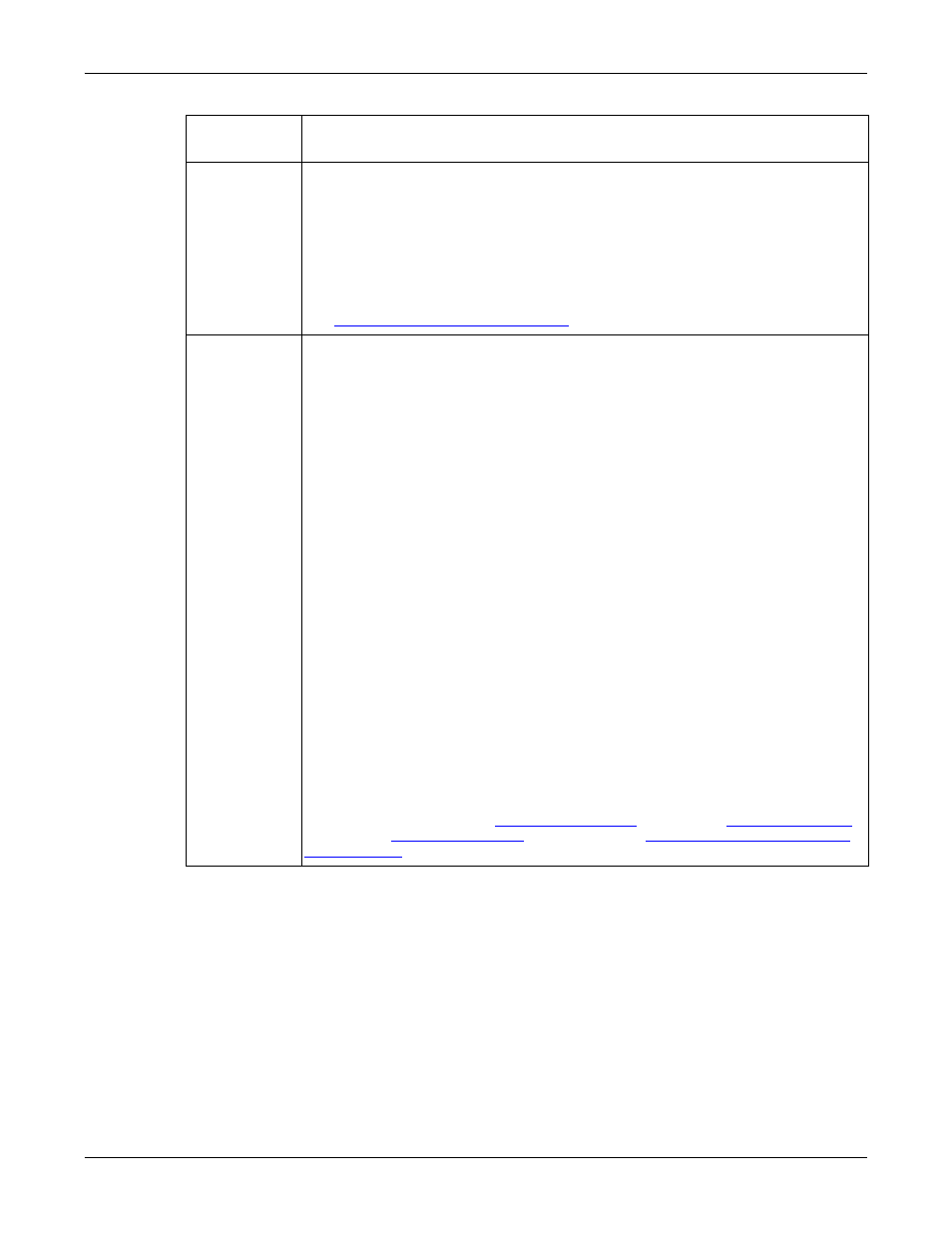
Understanding Security Methods and Terminology
Digital
Certificate
A digital certificate is an electronic credit card that establishes your
credentials when doing business or other transactions on the Web. It is issued
by a certification authority (CA). It contains your name, a serial number,
expiration dates, a copy of the certificate holder's public key (used for
encrypting messages and digital signatures), and the digital signature of the
certificate-issuing authority so that a recipient can verify that the certificate is
real. Some digital certificates conform to a standard, X.509. Digital certificates
can be kept in registries so that authenticating users can look up other users'
public keys.
Key and Certificate Management
on Page 61 for more information.
PKI (public
key
infrastructure)
A public key infrastructure (PKI) enables users of a basically unsecure public
network such as the Internet to securely and privately exchange data and
money through the use of a public and a private cryptographic key pair that is
obtained and shared through a trusted authority. The public key
infrastructure provides for a digital certificate that can identify an individual
or an organization and directory services that can store and, when necessary,
revoke the certificates. Although the components of a PKI are generally
understood, a number of different vendor approaches and services are
emerging. Meanwhile, an Internet standard for PKI is being worked on.
The public key infrastructure assumes the use of public key cryptography,
which is the most common method on the Internet for authenticating a
message sender or encrypting a message. Traditional cryptography has
usually involved the creation and sharing of a secret key for the encryption
and decryption of messages. This secret or private key system has the
significant flaw that if the key is discovered or intercepted by someone else,
messages can easily be decrypted. For this reason, public key cryptography
and the public key infrastructure is the preferred approach on the Internet.
(The private key system is sometimes known as symmetric cryptography and
the public key system as asymmetric cryptography.)
A public key infrastructure consists of:
•
A certificate authority (CA) that issues and verifies digital certificate. A
certificate includes the public key or information about the public key
•
A registration authority (RA) that acts as the verifier for the certificate
authority before a digital certificate is issued to a requestor
•
One or more directories where the certificates (with their public keys) are
held
•
A certificate management system
For more information, see
on Page 56, and
Term or
Issue
Explanation
