5 secure shell (ssh), Ssh configuration, Ssh algorithm – Allied Telesis AT-9724TS User Manual
Page 146
7-5 Secure Shell (SSH)
SSH is an abbreviation of Secure Shell, which is a program allowing secure remote login and secure network services over an insecure network. It allows a
secure login to remote host computers, a safe method of executing commands on a remote end node, and will provide secure encrypted and authenticated
communication between two non-trusted hosts. SSH, with its array of unmatched security features is an essential tool in today’s networking environment. It is a
powerful guardian against numerous existing security hazards that now threaten network communications.
The steps required to use the SSH protocol for secure communication between a remote PC (the SSH client) and the Switch (the SSH server) are as follows:
1.
Create a user account with admin-level access using the User Accounts window in the Security Management folder.This is identical to creating any
other admin-level User Account on the Switch, including specifying a password.This password is used to logon to the Switch, once a secure
communication path has been established using the SSH protocol.
2.
Configure the User Account to use a specified authorization method to identify users that are allowed to establish SSH connections with the Switch
using the SSH User Authentication window.There are three choices as to the method SSH will use to authorize the user, which are Host
Based, Password and Public Key.
3.
Configure the encryption algorithm that SSH will use to encrypt and decrypt messages sent between the SSH client and the SSH server, using the SSH
Algorithm window.
4.
Finally, enable SSH on the Switch using the SSH Configuration window.
After completing the preceding steps, a SSH Client on a remote PC can be configured to manage the Switch using a secure, in band connection.
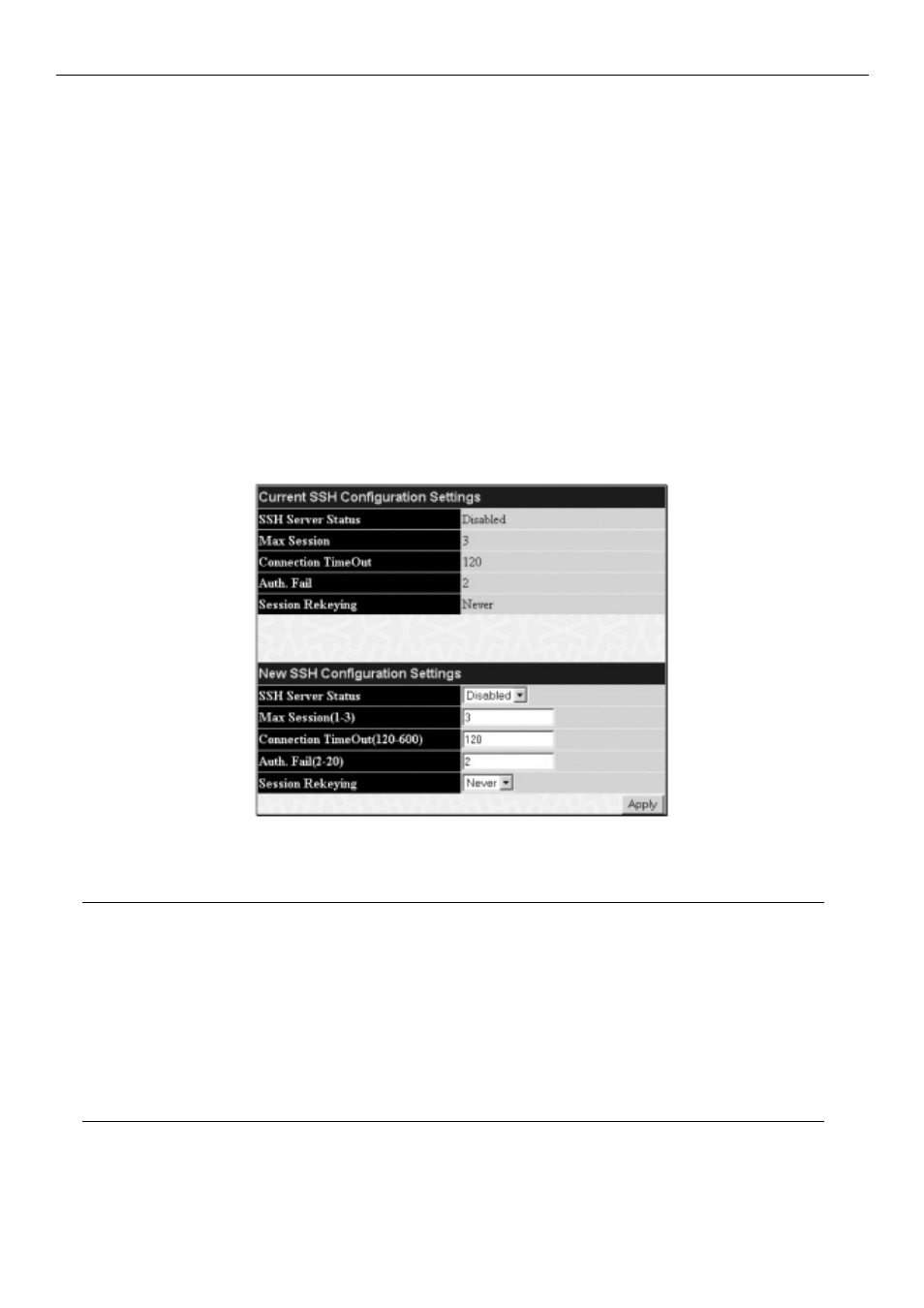
SSH Configuration
The following window is used to configure and view settings for the SSH server and can be opened by clicking Security Management > Secure Shell
(SSH) > SSH Configuration:
Figure 7- 23. Current and New SSH Configuration Settings
To configure the SSH server on the Switch, modify the following parameters and click Apply:
Parameter
Description
SSH Server Status
Use the pull-down menu to enable or disable SSH on the Switch.The default is Disabled.
Max Session (1-3)
Enter a value between 1 and 3 to set the number of users that may simultaneously access the Switch.The
default setting is 3.
Connection TimeOut (120-600) Allows the user to set the connection timeout.The use may set a time between 120 and 600 seconds.The
default setting is 120 seconds.
Auth. Fail (2-20)
Allows the Administrator to set the maximum number of attempts that a user may try to log on to the SSH
Server utilizing the SSH authentication.After the maximum number of attempts has been exceeded, the Switch
will be disconnected and the user must reconnect to the Switch to attempt another login.The number of
maximum attempts may be set between 2 and 20.The default setting is 2.
Session Rekeying
This field is used to set the time period that the Switch will change the security shell encryptions by using the
pull-down menu.The available options are Never, 10 min, 30 min, and 60 min.The default setting is Never.
SSH Algorithm
The SSH Algorithm window allows the configuration of the desired types of SSH algorithms used for authentication encryption.There are three categories of
algorithms listed and specific algorithms of each may be enabled or disabled by using their corresponding pull-down menus.All algorithms are enabled by default.
To open the following window, click Security Management > Secure Shell (SSH) > SSH Algorithm:
145
Allied Telesyn AT-9724TS High-Density Layer 3 Stackable Gigabit Ethernet Switch
