Encapsulation, Ipsec and nat, 3 encapsulation – ZyXEL Communications ZyXEL ZyWALL 2WE User Manual
Page 293: 4 ipsec and nat
ZyWALL 2 and ZyWALL 2WE
Introduction to IPSec
26-5
26.3 Encapsulation
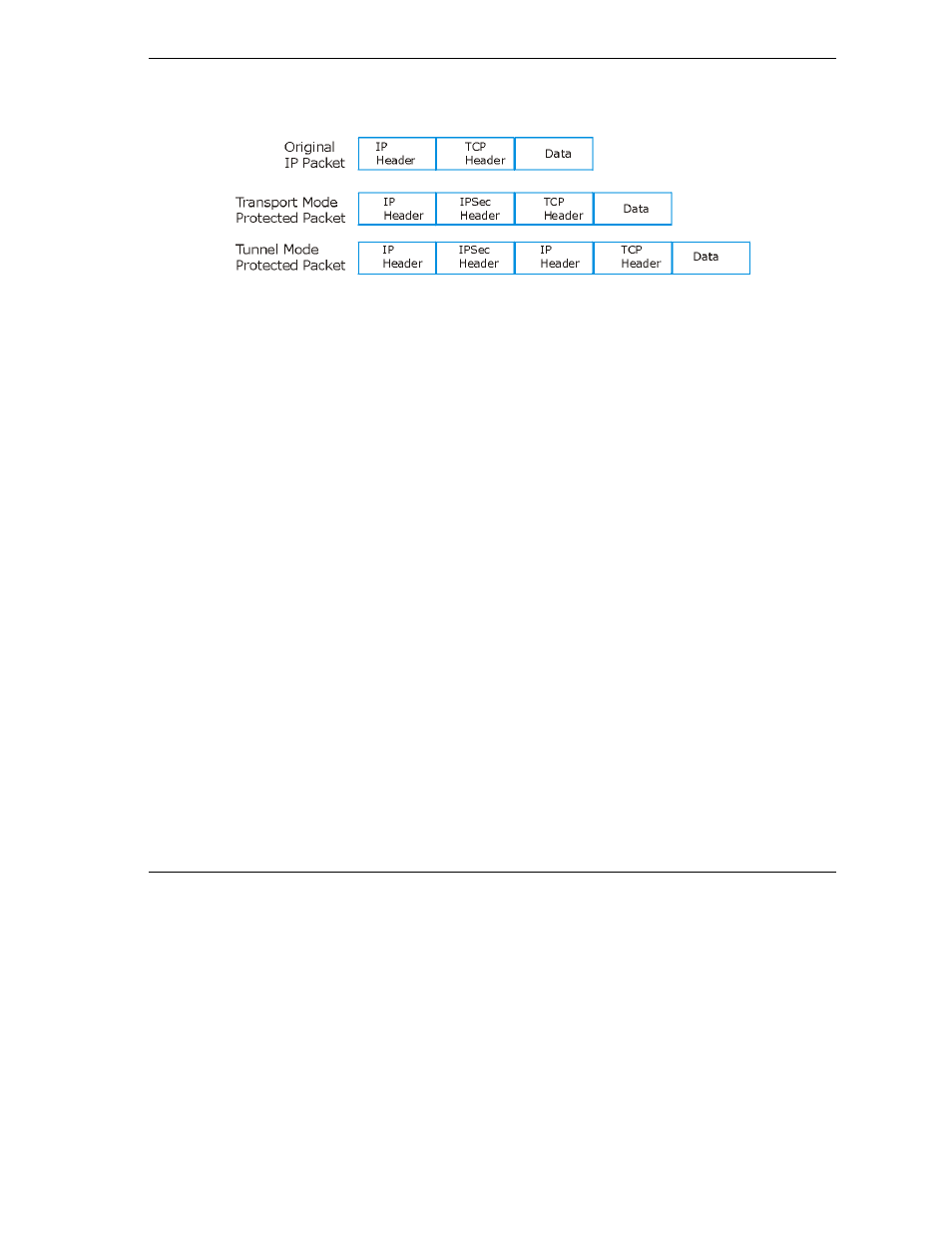
The two modes of operation for IPSec VPNs are Transport mode and Tunnel mode.
Figure 26-4 Transport and Tunnel Mode IPSec Encapsulation
26.3.1 Transport Mode
Transport mode is used to protect upper layer protocols and only affects the data in the IP packet. In
Transport mode, the IP packet contains the security protocol (AH or ESP) located after the original IP
header and options, but before any upper layer protocols contained in the packet (such as TCP and UDP).
With ESP, protection is applied only to the upper layer protocols contained in the packet. The IP header
information and options are not used in the authentication process. Therefore, the originating IP address
cannot be verified for integrity against the data.
With the use of AH as the security protocol, protection is extended forward into the IP header to verify the
integrity of the entire packet by use of portions of the original IP header in the hashing process.
26.3.2 Tunnel Mode
Tunnel mode encapsulates the entire IP packet to transmit it securely. A Tunnel mode is required for
gateway services to provide access to internal systems. Tunnel mode is fundamentally an IP tunnel with
authentication and encryption. This is the most common mode of operation. Tunnel mode is required for
gateway to gateway and host to gateway communications. Tunnel mode communications have two sets of IP
headers:
Outside header: The outside IP header contains the destination IP address of the VPN gateway.
Inside header: The inside IP header contains the destination IP address of the final system behind
the VPN gateway. The security protocol appears after the outer IP header and before the inside IP
header.
26.4 IPSec and NAT
Read this section if you are running IPSec on a host computer behind the ZyWALL.
NAT is incompatible with the AH protocol in both Transport and Tunnel mode. An IPSec VPN using the
AH protocol digitally signs the outbound packet, both data payload and headers, with a hash value appended
to the packet. When using AH protocol, packet contents (the data payload) are not encrypted.
