Tunneled authentication, Tunneled authentication -7, Table 4-6 – Symbol Technologies VC5090 User Manual
Page 83
Wireless Applications
4 - 7
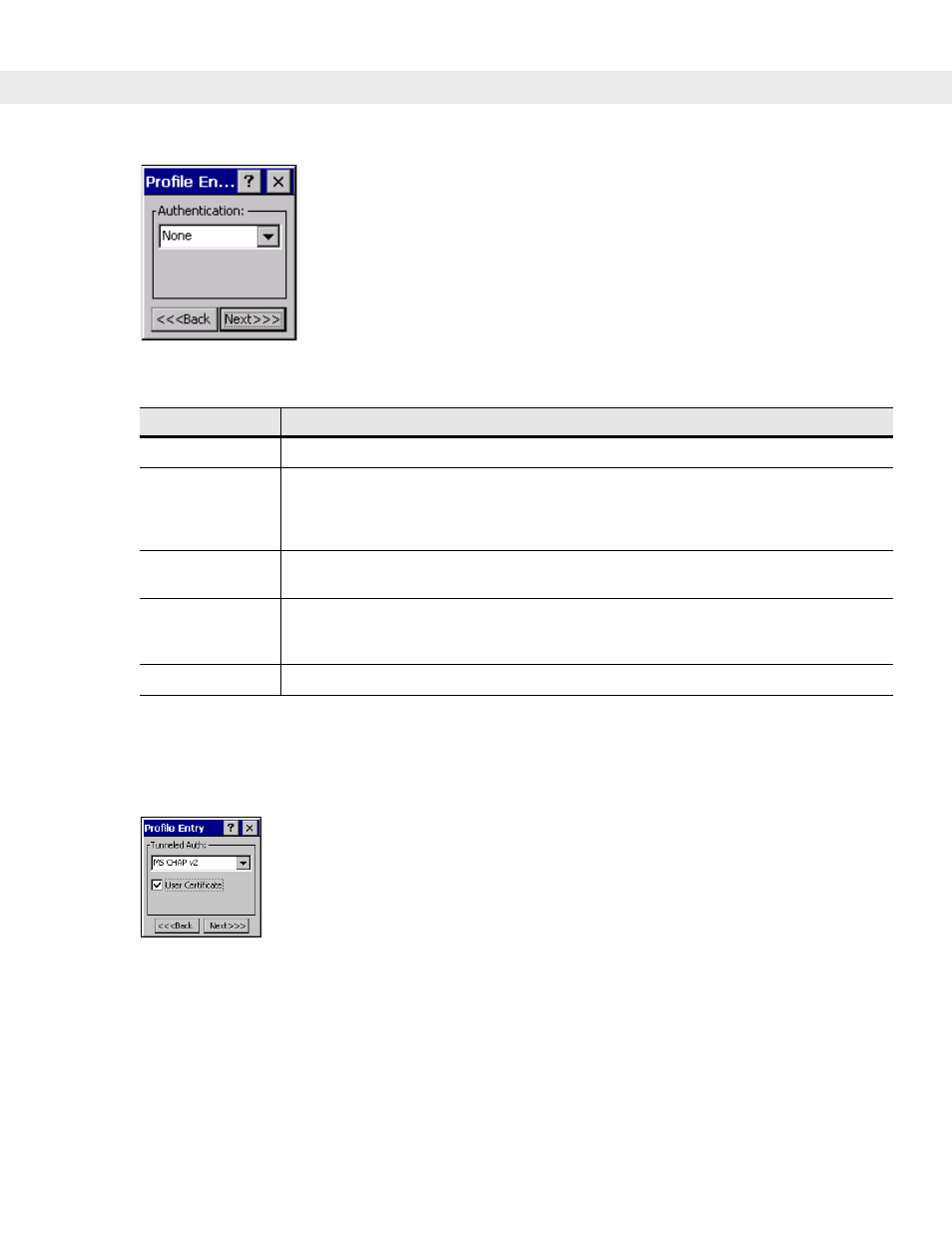
Figure 4-6
Authentication Dialog Box
Tunneled Authentication
Use the
Tunneled Authentication
dialog box to select the tunneled authentication options. There are different
selections available for PEAP or TTLS authentication.
Figure 4-7
Tunneled Authentication Dialog Box
To select a tunneled authentication type:
1.
Select a tunneled authentication type from the drop-down list. See
2.
Select the
User Certificate
check box if a certificate is required. If you selected the TLS tunnel type that
requires a user certificate, the check box is already selected.
3.
Tap
Next
. The
Installed User Certificates
dialog box appears.
Table 4-6
Authentication Options
Authentication
Description
None
Default setting when authentication is not required on the network.
EAP TLS
Select this option to enable EAP TLS authentication. EAP TLS is an authentication
scheme through IEEE 802.1x. It authenticates users and ensures only valid users can
connect to the network. It also restricts unauthorized users from accessing transmitted
information by using secure authentication certificates.
PEAP
Select this option to enable PEAP authentication. This method uses a digital certificate
to verify and authenticate a user's identity.
LEAP
Select this option to enable LEAP authentication, which is based on mutual
authentication. The AP and the connecting mobile computer require authentication
before gaining access to the network.
TTLS
Select this option to enable TTLS authentication.
