Configuring tcp attack protection, Overview, Enabling the syn cookie feature – H3C Technologies H3C SecPath F1000-E User Manual
Page 59
51
Configuring TCP attack protection
Overview
An attacker can attack the device during the process of TCP connection establishment. To prevent such
attacks, the device provides the following features:
•
SYN Cookie
•
Protection against Naptha attacks
This document describes the attacks these features can prevent, working mechanisms of these features,
and configuration procedures.
Enabling the SYN Cookie feature
As a general rule, the establishment of a TCP connection involves the following three handshakes.
1.
The request originator sends a SYN message to the target server.
2.
After receiving the SYN message, the target server establishes a TCP connection in the
SYN_RECEIVED state, returns a SYN ACK message to the originator, and waits for a response.
3.
After receiving the SYN ACK message, the originator returns an ACK message, establishing the
TCP connection.
Attackers may mount SYN Flood attacks during TCP connection establishment. They send a large number
of SYN messages to the server to establish TCP connections, but they never make any response to SYN
ACK messages. As a result, a large number of incomplete TCP connections are established, resulting in
heavy resource consumption and making the server unable to handle services normally.
The SYN Cookie feature can prevent SYN Flood attacks. After receiving a TCP connection request, the
server directly returns a SYN ACK message, instead of establishing an incomplete TCP connection. Only
after receiving an ACK message from the client can the server establish a connection, and then enter the
ESTABLISHED state. In this way, incomplete TCP connections could be avoided to protect the server
against SYN Flood attacks.
To enable the SYN Cookie feature:
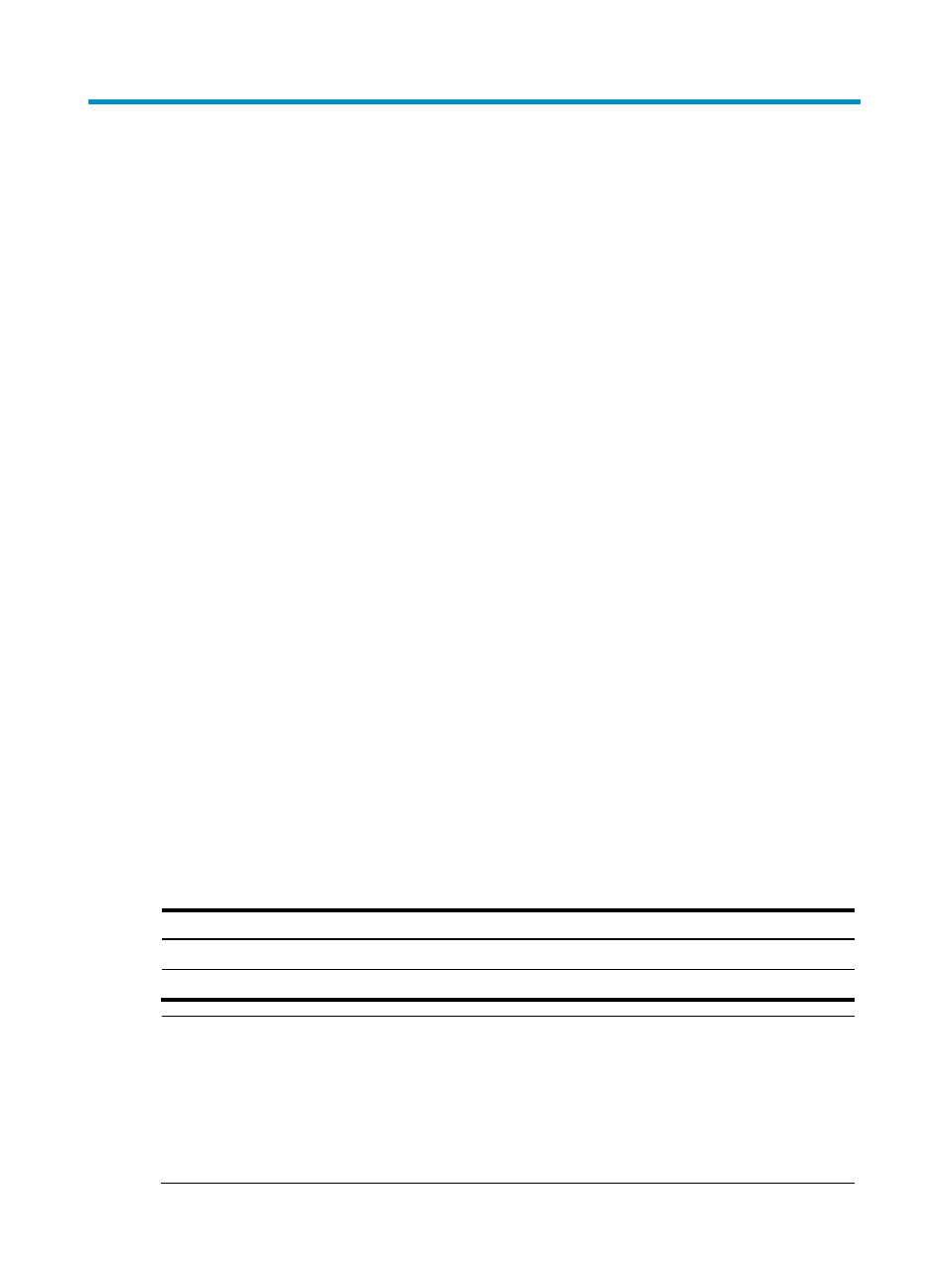
Step Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enable the SYN Cookie feature.
tcp syn-cookie enable
Enabled by default
NOTE:
•
If you enable MD5 authentication for TCP connections, the SYN Cookie configuration is ineffective.
Then, if you disable MD5 authentication for TCP connections, the SYN Cookie configuration
automatically becomes effective. For more information about MD5 authentication, see
Network
Management Configuration Guide.
•
With the SYN Cookie feature enabled, only the maximum segment size (MSS), is negotiated during TCP
connection establishment, instead of the window’s zoom factor and timestamp.
- H3C SecPath F5000-A5 Firewall H3C SecPath F1000-A-EI H3C SecPath F1000-E-SI H3C SecPath F1000-S-AI H3C SecPath F5000-S Firewall H3C SecPath F5000-C Firewall H3C SecPath F100-C-SI H3C SecPath F1000-C-SI H3C SecPath F100-A-SI H3C SecBlade FW Cards H3C SecBlade FW Enhanced Cards H3C SecPath U200-A U200-M U200-S H3C SecPath U200-CA U200-CM U200-CS
