Network requirements, N in, Figure 20 – H3C Technologies H3C SecPath F1000-E User Manual
Page 28
20
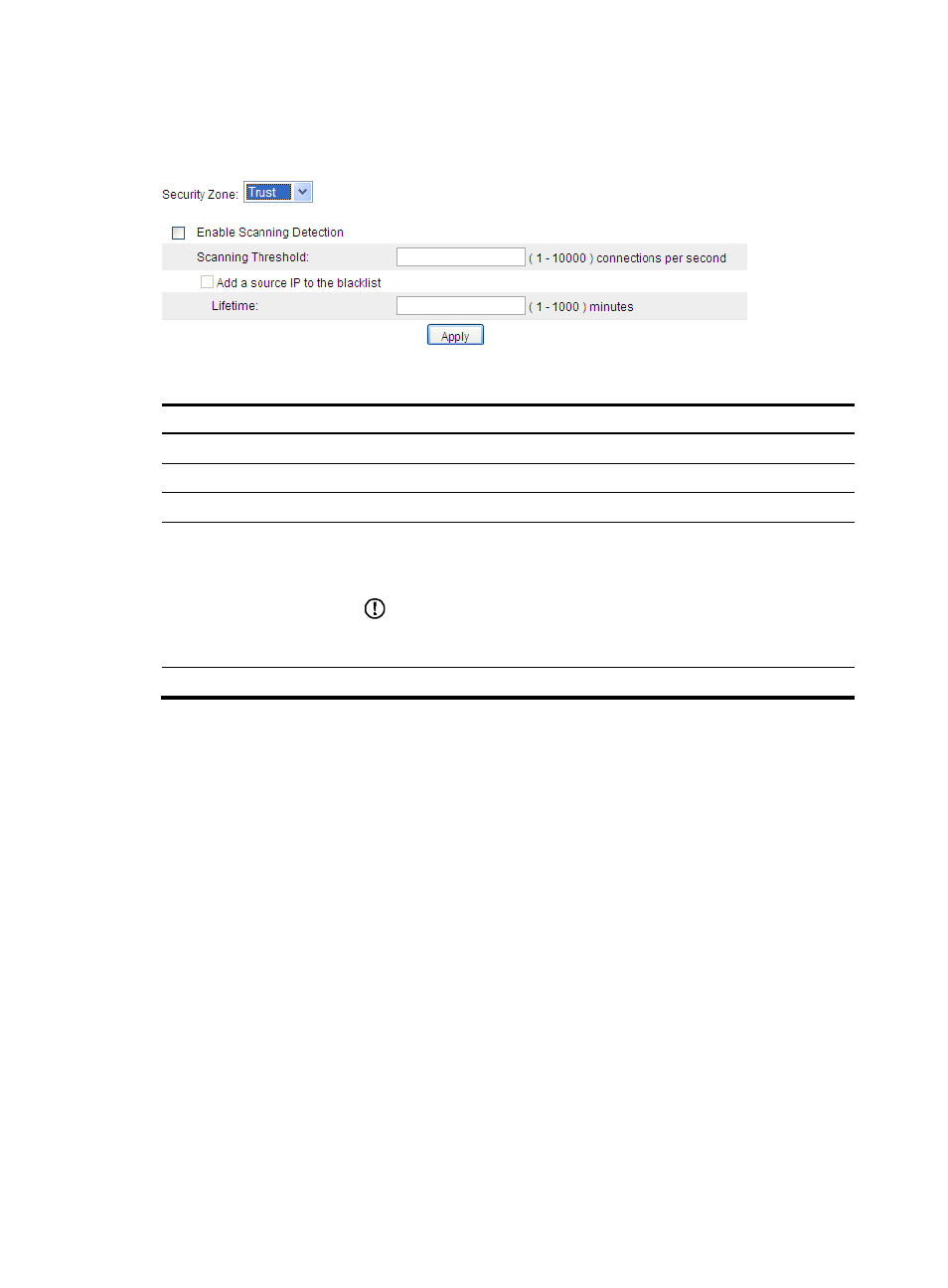
then view and configure the scanning detection rule for the security zone.
lists the scanning
detection configuration items.
Figure 20 Scanning detection configuration page
Table 10 Configuration items
Item
Description
Security Zone
Select a security zone to perform scanning detection configuration for it.
Enable Scanning Detection
Select this option to enable scanning detection for the security zone.
Scanning Threshold
Set the maximum connection rate for a source IP address.
Add a source IP to the
blacklist
Select this option to allow the system to blacklist a suspicious source IP address.
If this option is selected, you can then set the lifetime of the blacklisted source IP
addresses.
IMPORTANT:
Only when the blacklist feature is enabled, can the scanning detection function
blacklist a suspect and discard subsequent packets from the suspect.
Lifetime
Set the lifetime of the blacklist entry.
Traffic abnormality detection configuration
example
Network requirements
As shown in
, the internal network is the trusted zone, the subnet where the internal servers are
located is the demilitarized zone (DMZ), and the external network is the untrusted zone.
Configure SecPath to:
•
Protect the internal network against scanning attacks from the external network.
•
Limit the number of connections initiated by each internal host.
•
Limit the number of connections to the internal server.
•
Protect the internal server against SYN flood attacks from the external network.
- H3C SecPath F5000-A5 Firewall H3C SecPath F1000-A-EI H3C SecPath F1000-E-SI H3C SecPath F1000-S-AI H3C SecPath F5000-S Firewall H3C SecPath F5000-C Firewall H3C SecPath F100-C-SI H3C SecPath F1000-C-SI H3C SecPath F100-A-SI H3C SecBlade FW Cards H3C SecBlade FW Enhanced Cards H3C SecPath U200-A U200-M U200-S H3C SecPath U200-CA U200-CM U200-CS
