HP ProLiant Support Pack User Manual
Page 20
Introduction 20
•
The user does not temporarily disable BitLocker before flashing the System BIOS when using the
Microsoft BitLocker Drive Encryption.
•
The user has optionally selected to measure iLO, Smart Array, and NIC firmware.
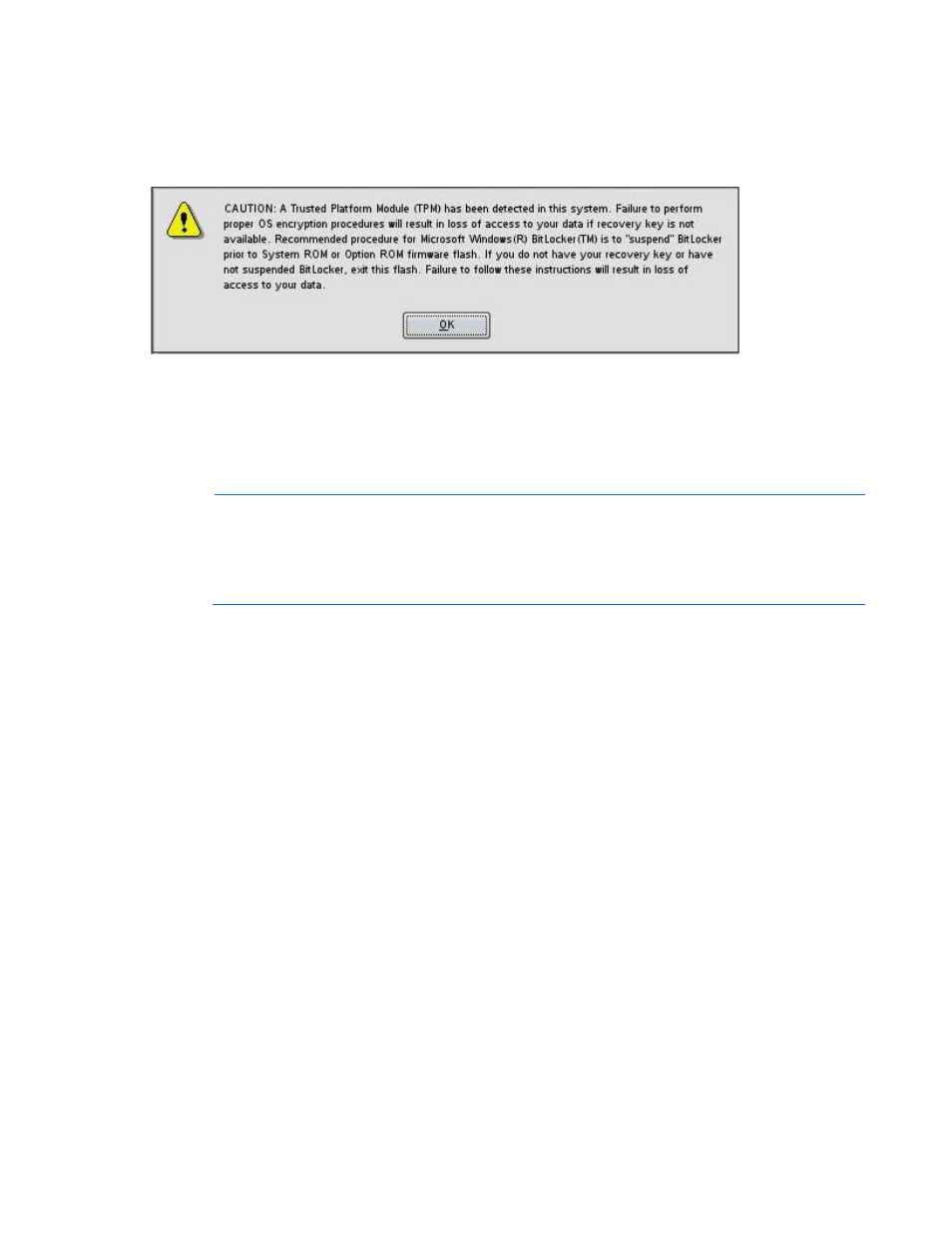
If HP Smart Update Manager detects a TPM, a pop-up warning message appears.
To enable firmware updates without the need to type in the TPM password on each server, the BitLocker
Drive Encryption must be temporarily disabled. Disabling the BitLocker Drive Encryption keeps the hard
drive data encrypted. However, BitLocker uses a plain text decryption key that is stored on the hard drive
to read the information. After the firmware updates have been completed, the BitLocker Drive Encryption
can be re-enabled. Once the BitLocker Drive Encryption has been re-enabled, the plain text key is
removed and BitLocker secures the drive again.
NOTE:
Temporarily disabling BitLocker Drive Encryption can compromise drive security and
should only be attempted in a secure environment. If you are unable to provide a secure
environment, HP recommends providing the boot password and leaving BitLocker Drive
Encryption enabled throughout the firmware update process. This requires the /tpmbypass
parameter for HP Smart Update Manager or the firmware update is blocked.
To temporarily disable BitLocker support to allow firmware updates, perform the following:
1.
Click Start, and then search for gpedit.msc in the Search Text box.
2.
When the Local Group Policy Editor starts, click Local Computer Policy.
3.
Click Computer Configuration>Administrative Templates>Windows Components>BitLocker Drive
Encryption.
4.
When the BitLocker settings are displayed, double-click Control Panel Setup: Enable Advanced
startup options.
5.
When the dialog box appears, click Disable.
