Appendix, Encryption algorithms – HP Secure Encryption User Manual
Page 70
Appendix 70
Appendix
Encryption algorithms
In keeping with the encryption standards outlined in FIPS 140-2
, controllers utilizing HP
Secure Encryption are designed to meet FIPS-140-2 Level 2 requirements by implementing both physical
security and cryptographic methods in protecting data-at-rest. Specifically, HP Secure Encryption satisfies the
cryptographic requirements established in FIPS 140-2 by using NIST-approved algorithms in protecting both
data and encryption keys. For more information, see the Cryptographic Algorithm Validation Program
website
.
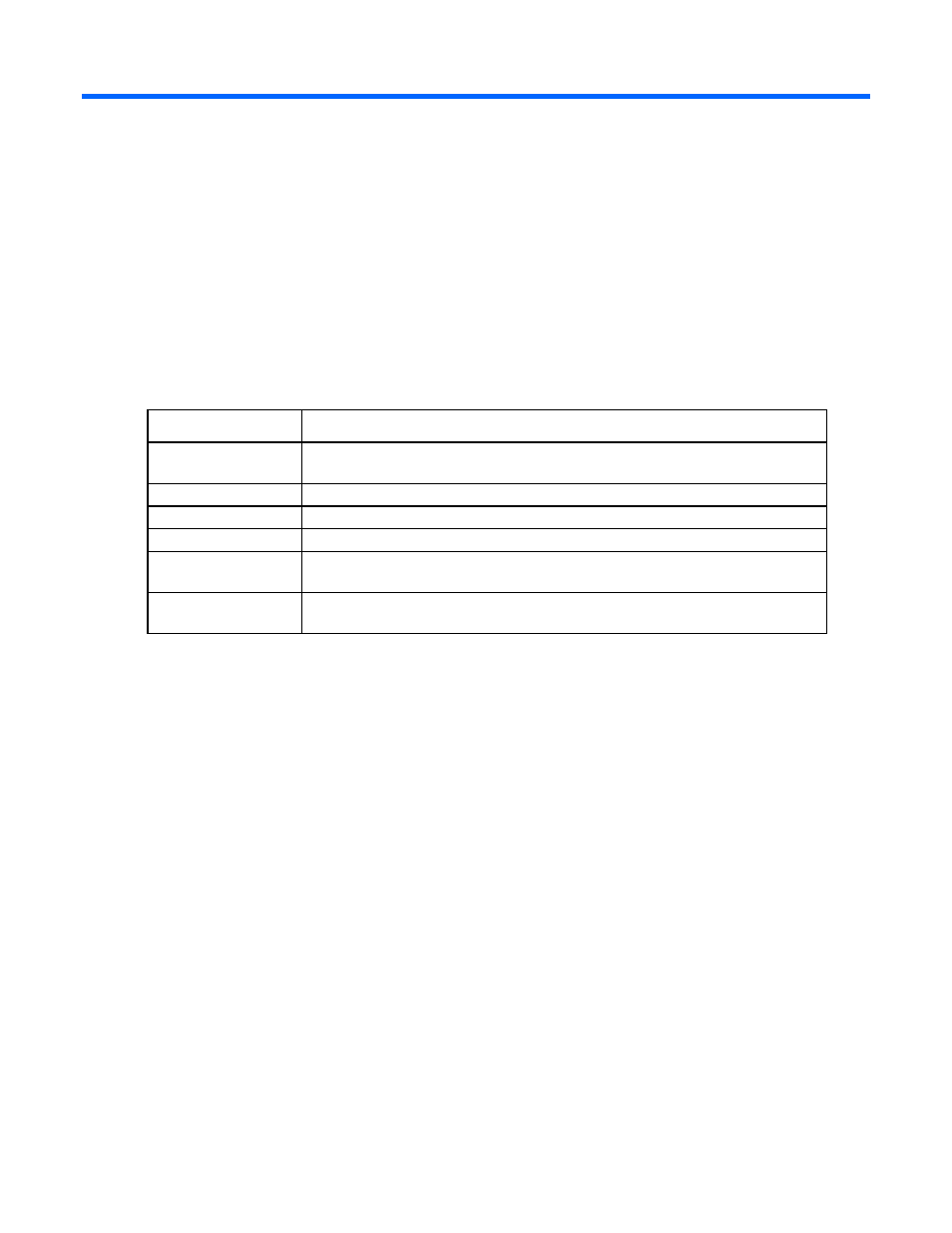
Algorithm
Description
XTS-AES 256-bit
The XTS algorithm is used to encrypt data on the drive platter as described in NIST
special publication SP 800-38E.
AES-ECB
The AES algorithm is used to perform symmetric key encryption.
SHA-256
The SHA secure hashing algorithms are described in FIPS 180-4.
HMAC
The HMAC algorithm is described in the FIPS 198-1 standard.
PBKDF2
The PBKDF2 algorithm derives cryptographic keying material from user-provided
passwords. The algorithm is described in NIST special publication SP 800-132.
DRBG
An implementation of the SP800-90A algorithm is used to produce random bit
sequences.
