2 data confidentiality, 3 data integrity, 4 data origin authentication – ZyXEL Communications P-334 User Manual
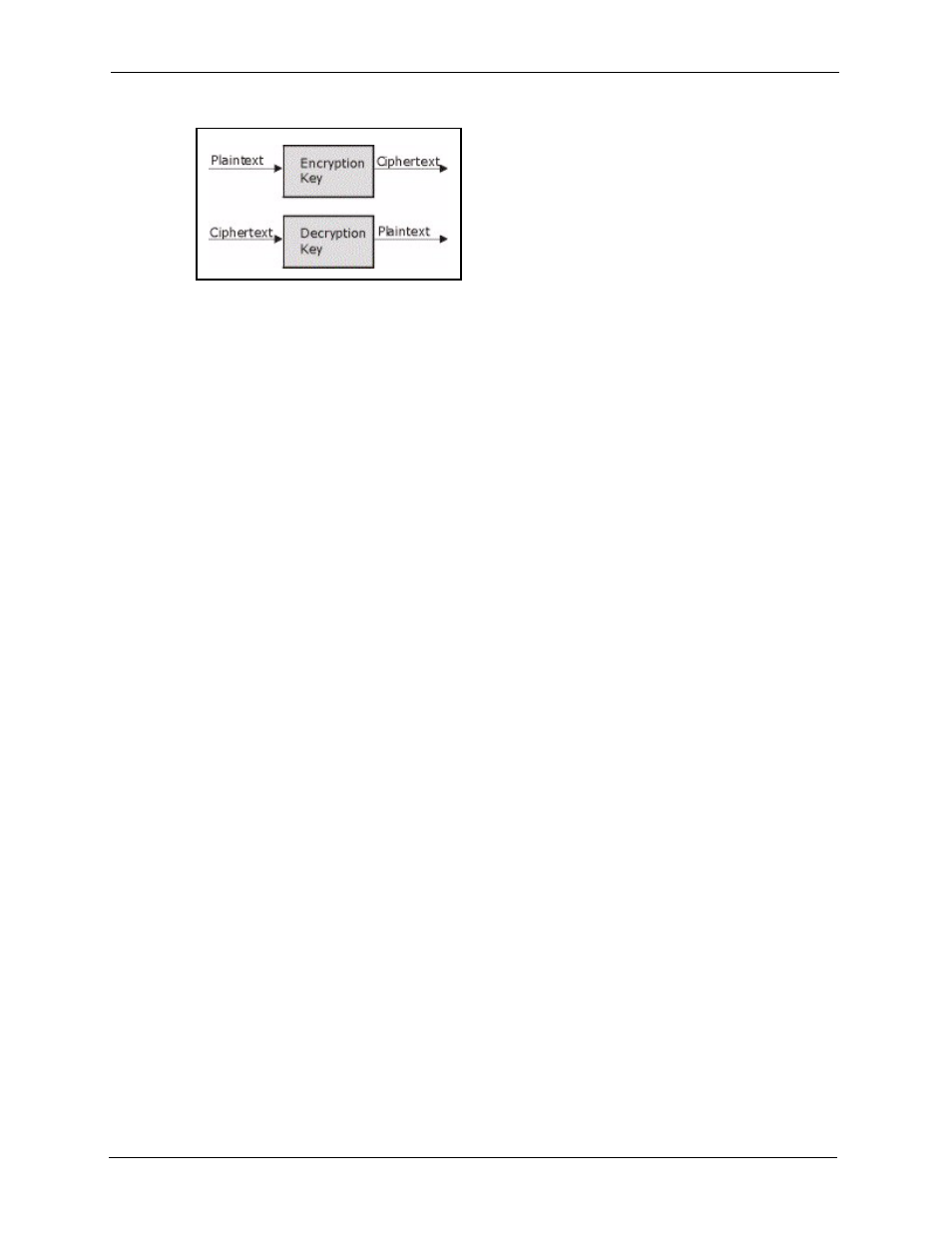
Page 152: 4 vpn applications, 2 ipsec architecture, Figure 56 encryption and decryption
Prestige 334 User’s Guide
151
Chapter 14 Introduction to IPSec
Figure 56 Encryption and Decryption
14.1.3.2 Data Confidentiality
The IPSec sender can encrypt packets before transmitting them across a network.
14.1.3.3 Data Integrity
The IPSec receiver can validate packets sent by the IPSec sender to ensure that the data has not
been altered during transmission.
14.1.3.4 Data Origin Authentication
The IPSec receiver can verify the source of IPSec packets. This service depends on the data
integrity service.
14.1.4 VPN Applications
The Prestige supports the following VPN applications.
• Linking Two or More Private Networks Together
Connect branch offices and business partners over the Internet with significant cost
savings and improved performance when compared to leased lines between sites.
• Accessing Network Resources When NAT Is Enabled
When NAT is enabled, remote users are not able to access hosts on the LAN unless the
host is designated a public LAN server for that specific protocol. Since the VPN tunnel
terminates inside the LAN, remote users will be able to access all computers that use
private IP addresses on the LAN.
• Unsupported IP Applications
A VPN tunnel may be created to add support for unsupported emerging IP applications.
See the chapter on Getting to Know Your Prestige for an example of a VPN application.
14.2 IPSec Architecture
The overall IPSec architecture is shown as follows.
