Configuring security, Introduction, Authentication – Perle Systems 5500161-40 User Manual
Page 213: Chapter 9 configuring security
IOLAN SDS/SCS/STS/MDC User’s Guide, Version 4.0
213
Configuring Security
Chapter 9
9
Introduction
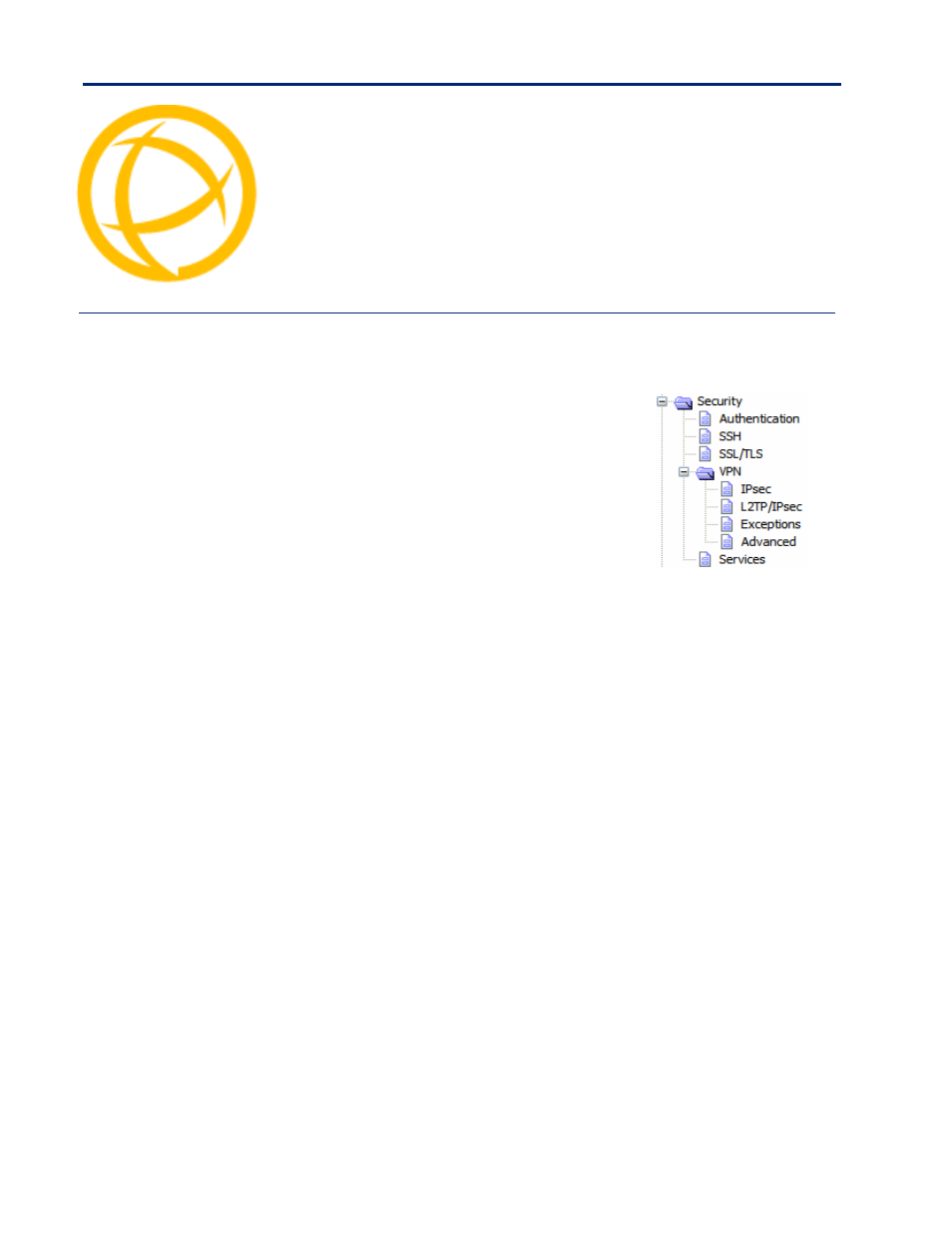
The
Security
group includes the following configuration options:
z
Authentication—When a serial port is configured for the
Console Management or TCP Sockets profile, the user can be
authenticated either locally in the IOLAN user profile or
externally. This option configures the external authentication
server. See
for more information.
z
SSH—This configuration window configures the SSH server in
the IOLAN. See
for more information.
z
SSL/TLS—This configuration window configures global
SSL/TLS settings, which can be overridden on the serial port
level. See
for more information.
z
VPN—This configuration window configures the Virtual Personal Network (VPN) IPsec and
L2TP/IPsec tunnel parameters. See
z
Services—This configuration window is used to enable/disabled client and daemon services that
run in the IOLAN. See
for more information.
Authentication
Authentication can be handled by the IOLAN or through an external authentication server.
Authentication is different from authorization, which can restrict a user’s access to the network
(although this can be done through the concept of creating sessions for a user, see
for more information). Authentication ensures that the user is defined within the
authentication database—with the exception of using the
Guest
authentication option under
Local
Authentication
, which can accept any user ID as long as the user knows the configured password.
For external authentication, the IOLAN supports RADIUS, Kerberos, LDAP, TACACS+, SecurID,
and NIS. You can specify a primary authentication method and a secondary authentication method. If
the primary authentication method fails (cannot connect to the server or authentication fails), the
secondary authentication method is tried (unless you enable the
Only Use as backup
option, in
which case the secondary authentication method will be tried only when the IOLAN cannot
communicate with the primary authentication host). This allows you to specify two different
authentication methods. If you do specify two different authentication methods, the user will be
prompted for his/her username once, but will be prompted for a password for each authentication
method tried. For example, user Alfred’s user ID is maintained in the secondary authentication
database, therefore, he will be prompted for his password twice, because he is not in the primary
authentication database.
Unlike the other external authentication methods, RADIUS and TACACS+ can also send back
Serial
Port
and
User
parameters that are used for the duration of the connection. Therefore, any parameters
configured by RADIUS or TACACS+ will override the same parameters configured in the IOLAN.
See
Appendix A, RADIUS and TACACS+ on page 347
for more information.
