Radius operation – IBM 12.1(22)EA6 User Manual
Page 98
5-18
Cisco Systems Intelligent Gigabit Ethernet Switch Modules for the IBM BladeCenter, Software Configuration Guide
24R9746
Chapter 5 Configuring Switch-Based Authentication
Controlling Switch Access with RADIUS
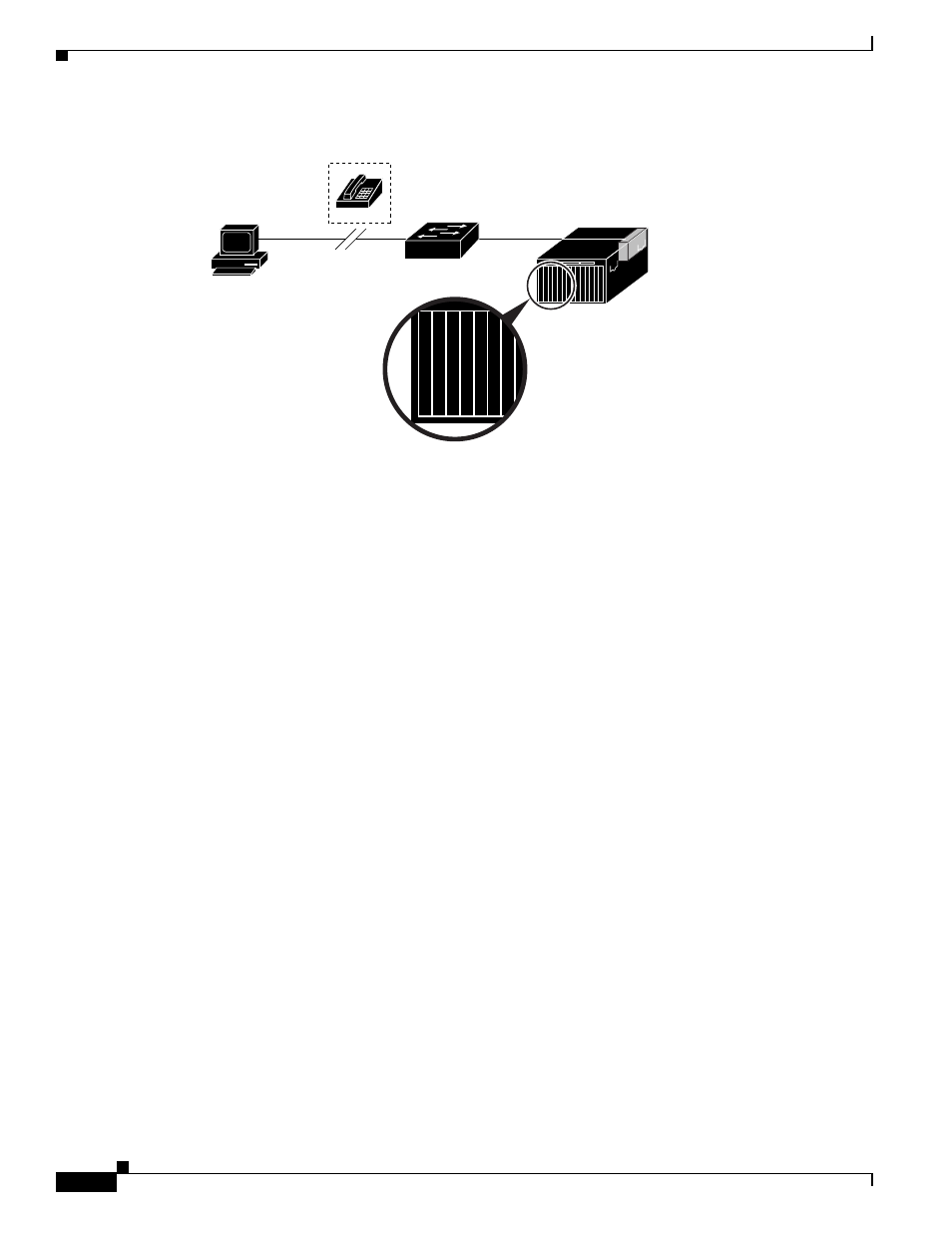
Figure 5-2
Transitioning from RADIUS to TACACS+ Services
RADIUS Operation
When a user attempts to log in and authenticate to a switch that is access controlled by a RADIUS server,
these events occur:
1.
The user is prompted to enter a username and password.
2.
The username and encrypted password are sent over the network to the RADIUS server.
3.
The user receives one of these responses from the RADIUS server:
a.
ACCEPT—The user is authenticated.
b.
REJECT—The user is either not authenticated and is prompted to re-enter the username and
password, or access is denied.
c.
CHALLENGE—A challenge requires additional data from the user.
d.
CHALLENGE PASSWORD—A response requests the user to select a new password.
The ACCEPT or REJECT response is bundled with additional data that is used for privileged EXEC or
network authorization. Users must first successfully complete RADIUS authentication before
proceeding to RADIUS authorization, if it is enabled. The additional data included with the ACCEPT or
REJECT packets includes these items:
•
Telnet, SSH, rlogin, or privileged EXEC services
•
Connection parameters, including the host or client IP address, access list, and user timeouts
92438
Catalyst 2950, 2955,
or 3550 switch
Remote
PC
RADIUS ser
v
e
r
RADIUS ser
v
e
r
T
A
CA
CS+ ser
v
e
r
T
A
CA
CS+ ser
v
e
r
BladeCenter
