Stateful inspection, 4 stateful inspection – ZyXEL Communications Broadband Security Gateway P-312 User Manual
Page 154
P312 Broadband Security Gateway
13-6
What Is a Firewall?
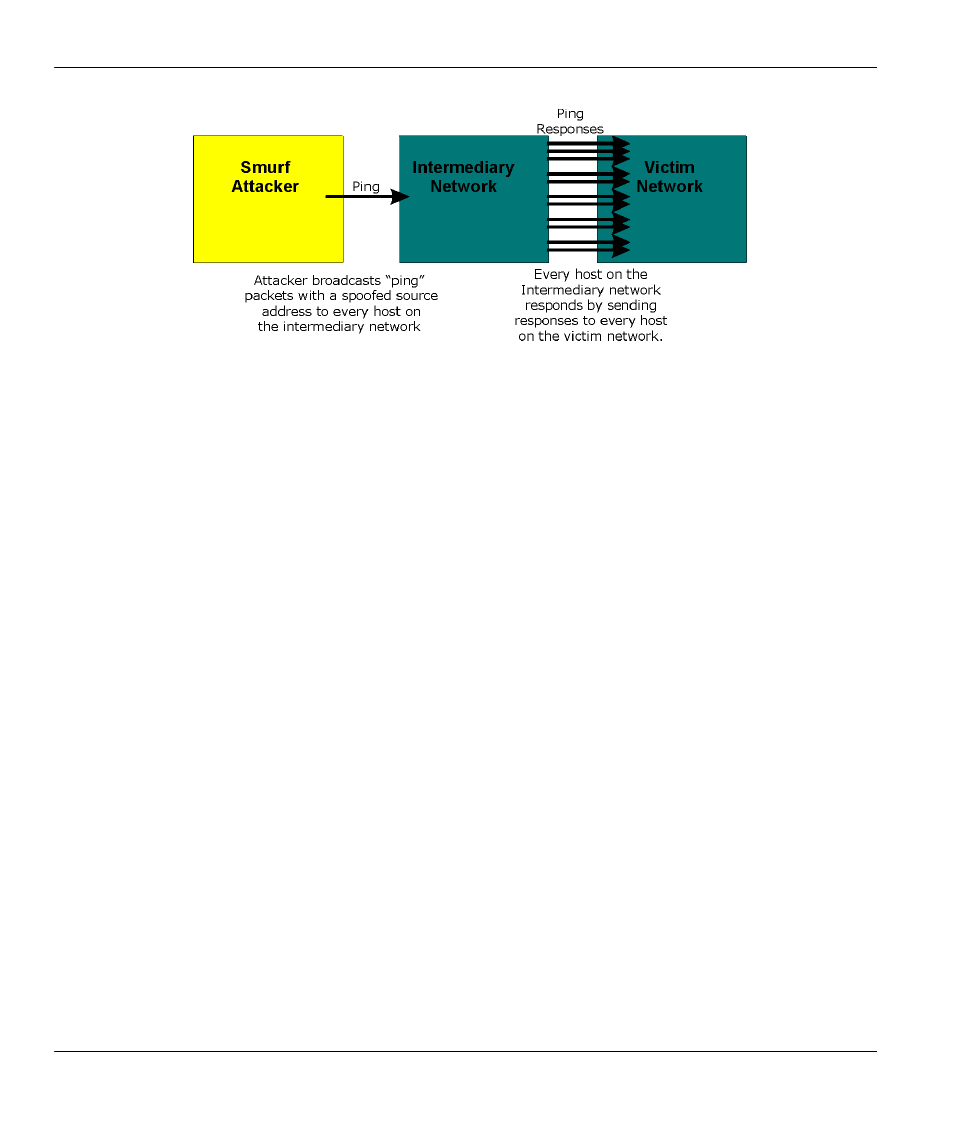
Figure 13-4
Smurf Attack
4. Often, many DoS attacks also employ a technique known as "IP Spoofing" as part of their attack. IP
Spoofing may be used to break into systems, to hide the hacker's identity, or to magnify the effect of the
DoS attack. IP Spoofing is a technique used to gain unauthorized access to computers by tricking a
router or firewall into thinking that the communications are coming from within the trusted network. To
engage in IP spoofing, a hacker must modify the packet headers so that it appears that the packets
originate from a trusted host and should be allowed through the router or firewall. The Prestige blocks all
IP Spoofing attempts.
13.4 Stateful Inspection
With stateful inspection, fields of the packets are compared to packets that are already known to be trusted.
For example, if you access some outside service, the proxy server remembers things about your original
request, like the port number and source and destination addresses. This “remembering” is called saving the
state. When the outside system responds to your request, the firewall compares the received packets with the
saved state to determine if they are allowed in. The Prestige uses stateful packet inspection to protect the
private LAN from hackers and vandals on the Internet. By default, the Prestige’s stateful inspection allows
all communications to the Internet that originate from the LAN, and blocks all traffic to the LAN that
originates from the Internet i.e.,
!
Allow all sessions originating from the LAN (local network) to the WAN (Internet)
!
Deny all sessions originating from the WAN (Internet) to the LAN (local network)
