ZyXEL Communications P-660HN-TxA User Manual
Page 217
Chapter 20 Logs
P-660HN-TxA User’s Guide
217
For type and code details, see
.
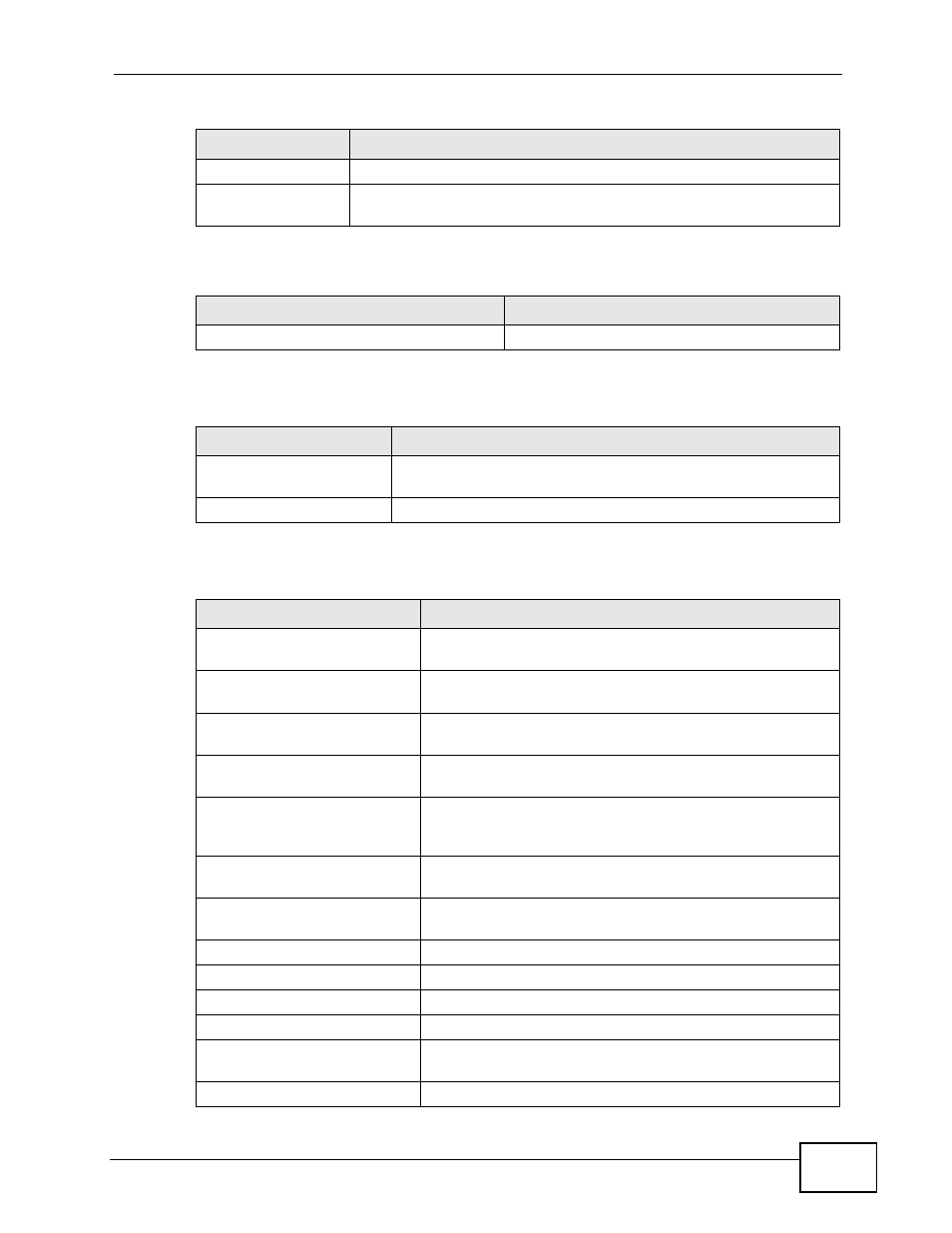
ppp:LCP Closing
The PPP connection’s Link Control Protocol stage is closing.
ppp:IPCP Closing
The PPP connection’s Internet Protocol Control Protocol stage is
closing.
Table 82 UPnP Logs
LOG MESSAGE
DESCRIPTION
UPnP pass through Firewall
UPnP packets can pass through the firewall.
Table 83 Content Filtering Logs
LOG MESSAGE
DESCRIPTION
%s: block keyword
The content of a requested web page matched a user defined
keyword.
%s
The system forwarded web content.
Table 84 Attack Logs
LOG MESSAGE
DESCRIPTION
attack [ TCP | UDP | IGMP
| ESP | GRE | OSPF ]
The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF
attack.
attack ICMP (type:%d,
code:%d)
The firewall detected an ICMP attack.
land [ TCP | UDP | IGMP |
ESP | GRE | OSPF ]
The firewall detected a TCP/UDP/IGMP/ESP/GRE/OSPF
land attack.
land ICMP (type:%d,
code:%d)
The firewall detected an ICMP land attack.
ip spoofing - WAN [ TCP |
UDP | IGMP | ESP | GRE |
OSPF ]
The firewall detected an IP spoofing attack on the WAN
port.
ip spoofing - WAN ICMP
(type:%d, code:%d)
The firewall detected an ICMP IP spoofing attack on the
WAN port.
icmp echo : ICMP
(type:%d, code:%d)
The firewall detected an ICMP echo attack.
syn flood TCP
The firewall detected a TCP syn flood attack.
ports scan TCP
The firewall detected a TCP port scan attack.
teardrop TCP
The firewall detected a TCP teardrop attack.
teardrop UDP
The firewall detected an UDP teardrop attack.
teardrop ICMP (type:%d,
code:%d)
The firewall detected an ICMP teardrop attack.
illegal command TCP
The firewall detected a TCP illegal command attack.
Table 81 PPP Logs (continued)
LOG MESSAGE
DESCRIPTION
