5 monitoring layer-2 security filters, 6 layer-2 filter examples, Monitoring layer-2 security filters -9 – Riverstone Networks WICT1-12 User Manual
Page 555: Layer-2 filter examples -9, Figure 25-1 source filter example -9
Riverstone Networks RS Switch Router User Guide Release 8.0 25-9
Security Configuration
Layer-2 Security Filters
To configure Layer-2 secure port filters, enter the following commands in Configure mode:
25.2.5
Monitoring Layer-2 Security Filters
The RS provides display of Layer-2 security filter configurations contained in the routing table.
To display security filter information, enter the following commands in Enable mode.
25.2.6
Layer-2 Filter Examples
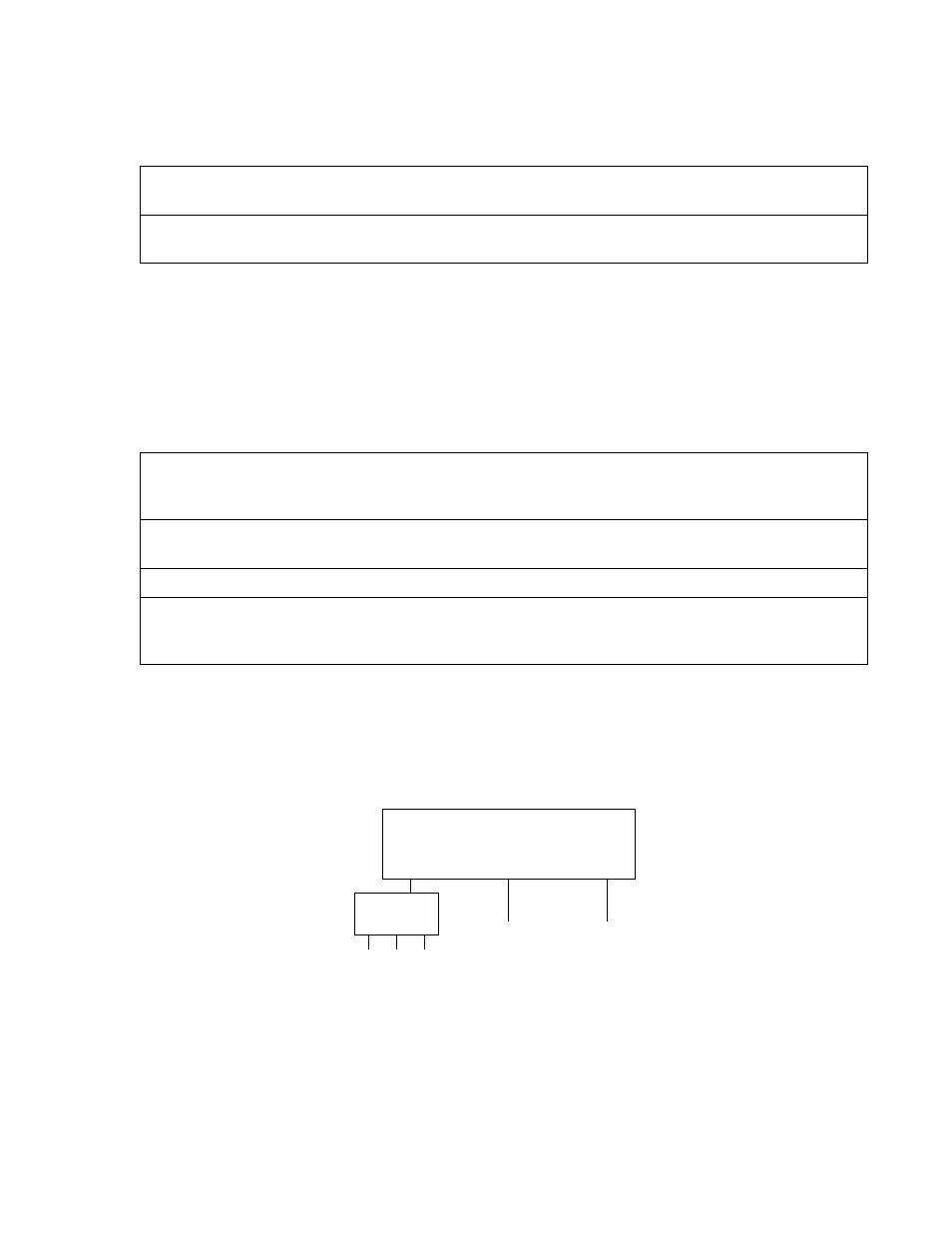
shows the router connections for which layer-2 security filters will be configured.
Figure 25-1 Source filter example
Configure a source secure port filter.
filters add secure-port name
direction source vlan
in-port-list
Configure a destination secure port
filter.
filters add secure-port name
direction destination
vlan
in-port-list
Show address filters.
filters show address-filter
[all-source|all-destination|all-flow] [source-mac
dest-mac
]
[ports
] [vlan
]
Show port address lock
filters.
filters show port-address-lock ports [ports
] [vlan
] [source-mac
]
Show secure port filters.
filters show secure-port
Show static entry filters.
filters show static-entry
[all-source|all-destination|all-flow] ports
vlan
[source-mac
dest-mac
]
et.1.1
et.1.2
et.1.3
Hub
Engineers,
Consultant
Engineering
File Servers
Finance
File Servers
Router
