2 arp inspection overview, Figure 99 example: man-in-the-middle attack, Ax b – ZyXEL Communications ES-3148 Series User Manual
Page 201
Chapter 24 IP Source Guard
ES-3148 User’s Guide
201
24.1.1.3 DHCP Relay Option 82 Information
The Switch can add information to DHCP requests that it does not discard. This provides the
DHCP server more information about the source of the requests. The Switch can add the
following information:
• Slot ID (1 byte), port ID (1 byte), and source VLAN ID (2 bytes)
• System name (up to 32 bytes)
This information is stored in an Agent Information field in the option 82 field of the DHCP
headers of client DHCP request frames. See
about DHCP relay option 82.
When the DHCP server responds, the Switch removes the information in the Agent
Information field before forwarding the response to the original source.
You can configure this setting for each source VLAN. This setting is independent of the
DHCP relay settings (
24.1.1.4 Configuring DHCP Snooping
Follow these steps to configure DHCP snooping on the Switch.
1 Enable DHCP snooping on the Switch.
2 Enable DHCP snooping on each VLAN, and configure DHCP relay option 82.
3 Configure trusted and untrusted ports, and specify the maximum number of DHCP
packets that each port can receive per second.
4 Configure static bindings.
24.1.2 ARP Inspection Overview
Use ARP inspection to filter unauthorized ARP packets on the network. This can prevent
many kinds of man-in-the-middle attacks, such as the one in the following example.
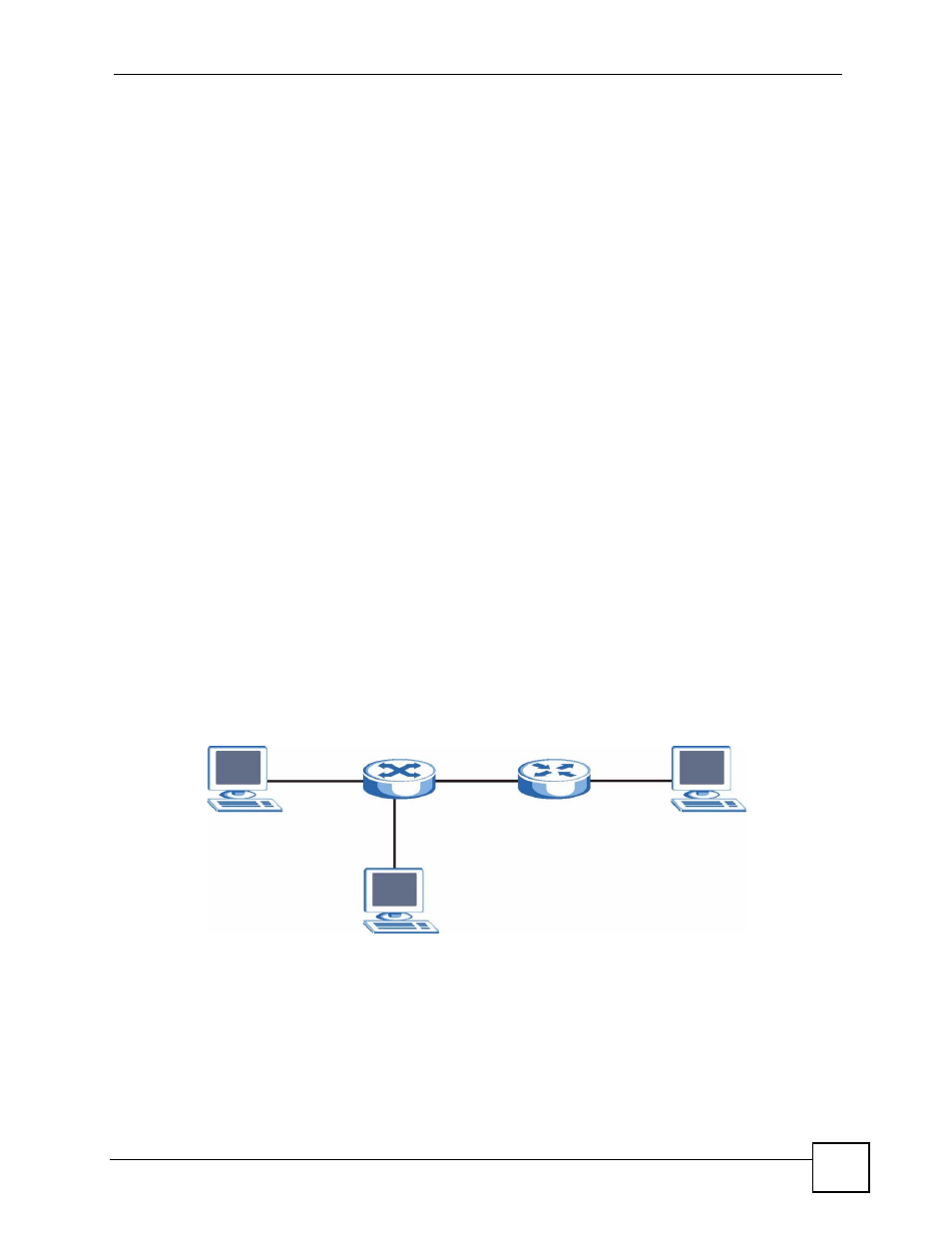
Figure 99 Example: Man-in-the-middle Attack
In this example, computer B tries to establish a connection with computer A. Computer X is in
the same broadcast domain as computer A and intercepts the ARP request for computer A.
Then, computer X does the following things:
• It pretends to be computer A and responds to computer B.
• It pretends to be computer B and sends a message to computer A.
As a result, all the communication between computer A and computer B passes through
computer X. Computer X can read and alter the information passed between them.
A
X
B
