3 network access server configuration – PLANET WGSD-10020 User Manual
Page 221
User’s Manual of WGSD-10020 Series
221
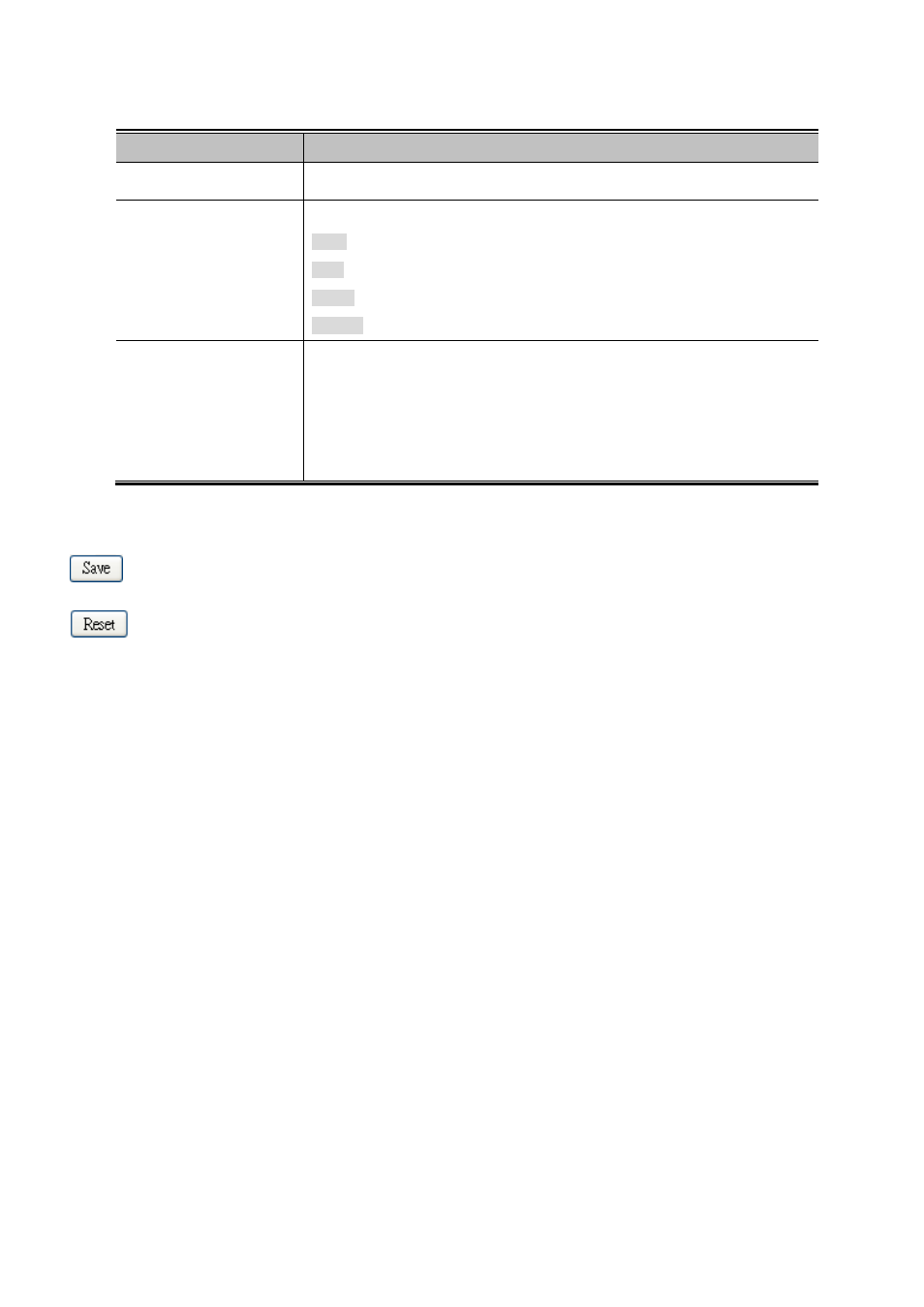
The page includes the following fields:
Object
Description
•
Client
The management client for which the configuration below applies.
•
Authentication Method
Authentication Method can be set to one of the following values:
None: authentication is disabled and login is not possible.
local: use the local user database on the switch stack for authentication.
radius: use a remotserver for authentication.
tacacs+: use a remotserver for authentication.
•
Fallback
Enable fallback to local authentication by checking this box.
If none of the configured authentication servers are alive, the local user database
is used for authentication.
This is only possible if the Authentication Method is set to something else than
'none or 'local'.
Buttons
: Click to save changes.
: Click to undo any changes made locally and revert to previously saved values.
4.11.3 Network Access Server Configuration
This page allows you to configure tand MAC-based authentication system and port settings.
The IEEE 802.1X standard defines a port-based access control procedure that prevents unauthorized access to a network by
requiring users to first submit credentials for authentication. One or more central servers, the backend servers, determine
whether the user is allowed access to the network. These backend (RADIUS) servers are configured on the
"Configuration→Security→AAA" page. The IEEE802.1X standard defines port-based operation, but non-standard variants
overcome security limitations as shall be explored below.
MAC-based authentication allows for authentication of more than one user on the same port, and doesn't require the user to
have special 802.1X supplicant software installed on his system. The switch uses the user's MAC address to authenticate
against the backend server. Intruders can create counterfeit MAC addresses, which makes MAC-based authentication less
secure than 802.1X authentication. The NAS configuration consists of two sections, a system- and a port-wide. The Network
Access Server Configuration screen in
Figure 4-11-4
appears.
