Trusted management servers category, Kerberos authentication category (windows only), Kerberos authentication procedure – HP Systems Insight Manager User Manual
Page 44
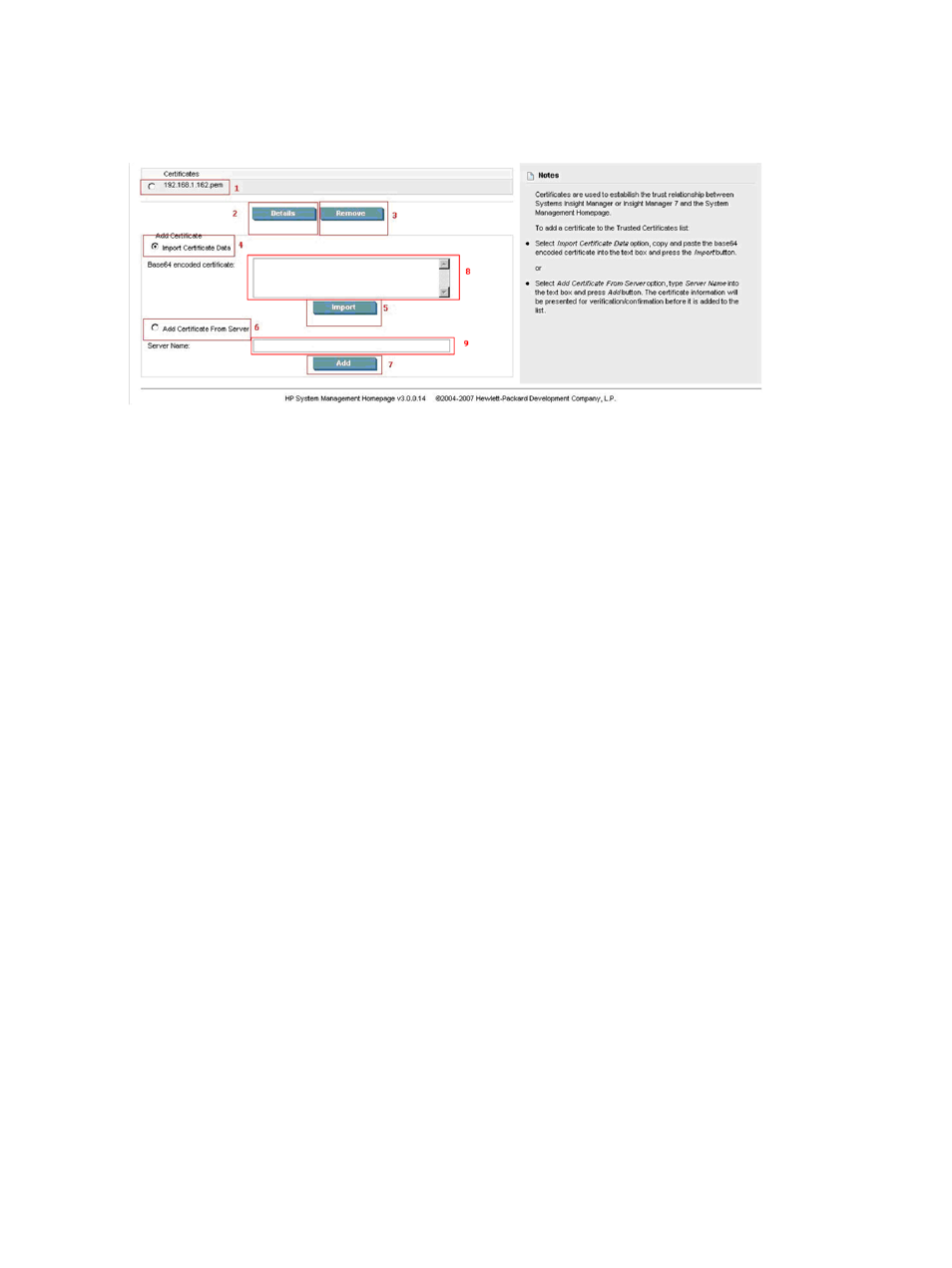
Trusted Management Servers category
establish the trust relationship between HP SIM or Insight Manager 7 and HP SMH. The Trusted
Management Servers link enables you to manage your
in the Trusted Certificates List. Note the
following:
To import a certificate to the trusted certificates list:
1.
Select Settings from the menu.
2.
In the System Management Homepage box, click the Security link.
3.
Click the Trusted Management Servers link.
4.
In the Add Certificate area, click the Import Certificate Data radio button.
5.
Copy and paste the Base64-encoded certificate into the textbox.
6.
Click Import.
To add a certificate from a server:
1.
Select Settings from the menu.
2.
In the System Management Homepage box, click the Security link.
3.
Click the Trusted Management Servers link.
4.
In the Add Certificate From Server area, click the Add Certificate From Server radio button.
5.
In the Server Name textbox, enter the IP address or server name of the HP SIM server.
6.
Click Add.
Kerberos Authentication category (Windows only)
is a trusted third-party network authentication protocol for client/server applications by using
secret-key cryptography developed at
. Kerberos allows different hosts and users to authenticate and
confirm the identity of each other.
One primary use of Kerberos is for offering
capability on secure networks. Usually in
a Kerberos environment users log in only once at the start of their sessions, acquiring Kerberos credentials
that are used transparently to log in on all other services available, such as SSH, FTP, and authenticated
web sessions.
A Kerberos domain is a
and is expressed in all capital letters. For example, the Kerberos realm for
smhkerberos.com is
SMHKERBEROS.COM.
are users and services/hosts that are present in a Kerberos realm and are allowed to authenticate
to each other. A
has a principal name such as group@REALM (for example, [email protected]),
and a service has a principal name like service/FQDN@REALM (for example,
HTTP/[email protected]
or
host/[email protected]
).
Kerberos Authentication Procedure
The following outlines the process when a user accesses secure services in a Kerberos realm.
The process only occurs when the user initially logs in to a Kerberos realm and tries to perform the first access
to a Kerberos-secured service.
44
The Settings Page
