Idm usage strategies, Idm usage strategies -4 – HP Identity Driven Manager Software Series User Manual
Page 22
Getting Started
Before You Begin
5. Create an Access Policy Group, with rules containing the Location, Time,
System, and Access Profile that is applied to users when they login. (See
page 3-16)
6. Assign Users to the appropriate Access Policy Group. (See page 3-20)
7. Deploy the configuration policies to the IDM Agent on the RADIUS server.
(See page 3-22)
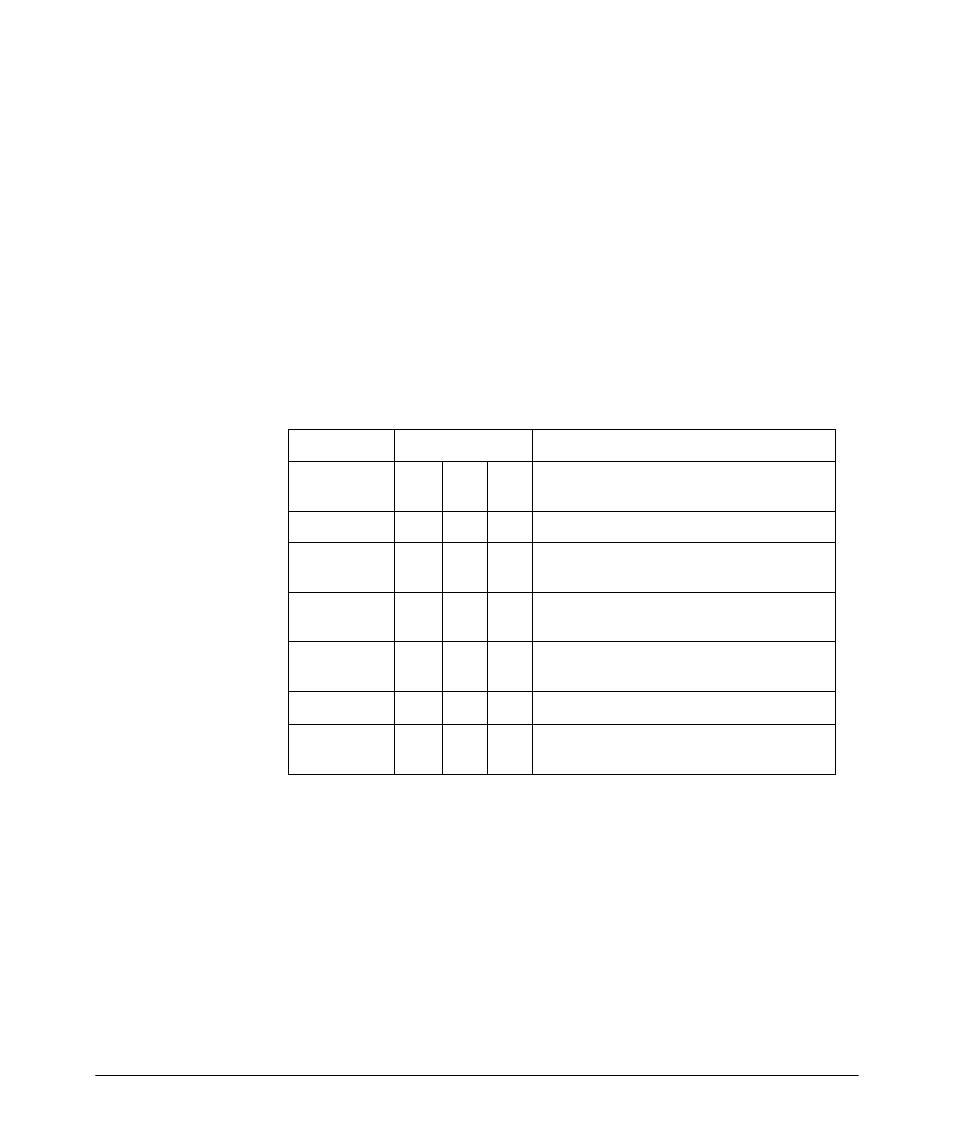
IDM Usage Strategies
You can use IDM to simply monitor user activity on the network, or to apply
user authentication rules to improve network security and performance. The
following table identifies the IDM configuration for various deployment and
usage strategies for IDM.
Authentication
Authorization
Strategy Description
VLAN QoS Rate-
Limit
Monitor and report user activity.
x
Enhance normal RADIUS authentication with
Location, Time, and System rules
x
x
Provide rudimentary VLAN segregation
(Unknown Users, Guests, Visitors, Contractors)
x
x
Provide complete VLAN placement for all
Users
x
x
x
Provide QoS and Rate-limits per User
x
x
x
x
VLAN, QoS, and Rate-limits for all users, based
on Location, Time, and System
Table 1. IDM Deployment and Usage strategies
2-4
