1 icmp vulnerability, 2 illegal commands (netbios and smtp), Figure 69 smurf attack – ZyXEL Communications Prestige 2602H Series User Manual
Page 172
Prestige 2602H/HW Series User’s Guide
172
Chapter 13 Firewalls
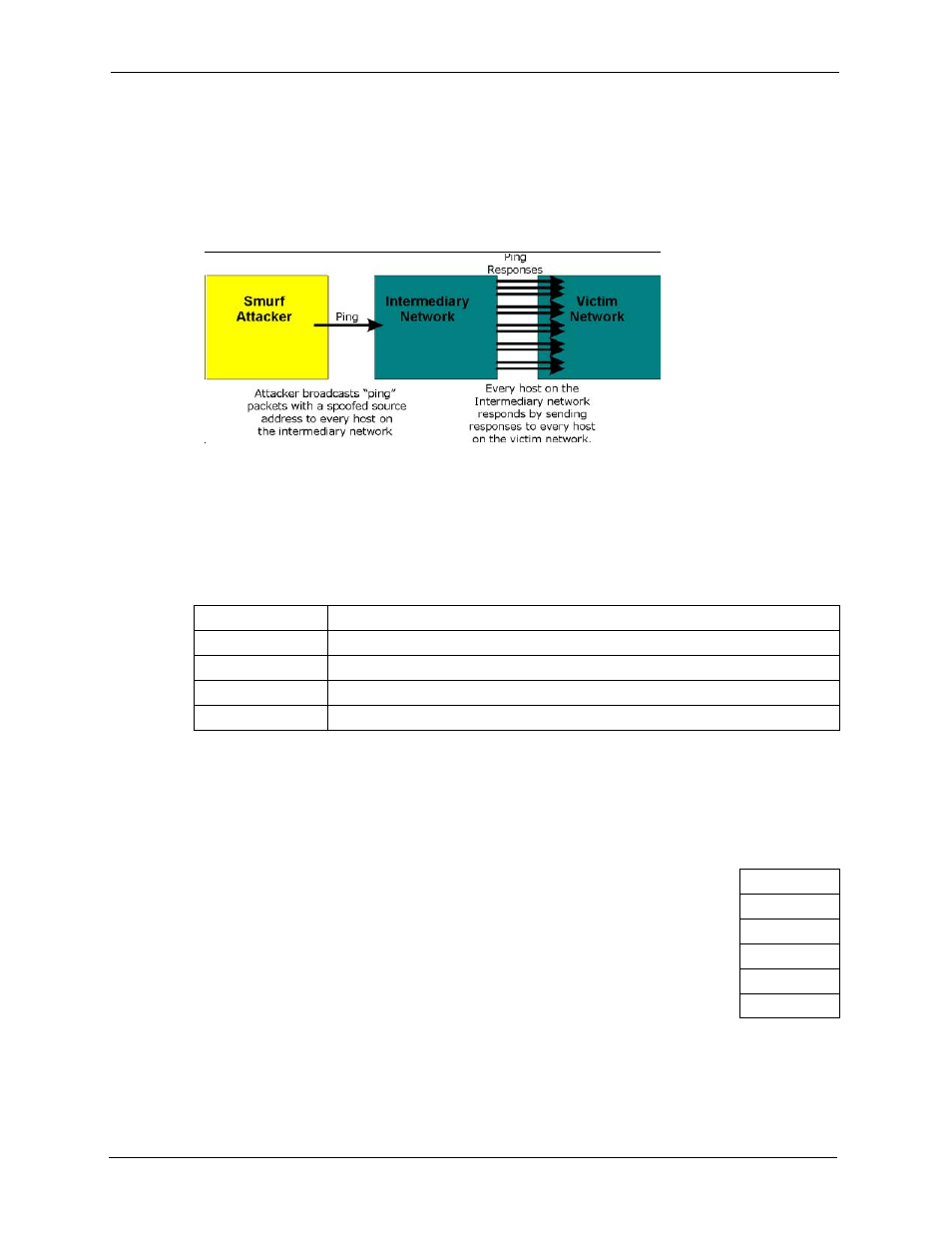
amount of ICMP echo request and response traffic. If a hacker chooses to spoof the
source IP address of the ICMP echo request packet, the resulting ICMP traffic will not
only clog up the "intermediary" network, but will also congest the network of the spoofed
source IP address, known as the "victim" network. This flood of broadcast traffic
consumes all available bandwidth, making communications impossible.
Figure 69 Smurf Attack
13.4.2.1 ICMP Vulnerability
ICMP is an error-reporting protocol that works in concert with IP. The following ICMP types
trigger an alert:
13.4.2.2 Illegal Commands (NetBIOS and SMTP)
The only legal NetBIOS commands are the following - all others are illegal.
All SMTP commands are illegal except for those displayed in the following tables.
Table 51 ICMP Commands That Trigger Alerts
5
REDIRECT
13
TIMESTAMP_REQUEST
14
TIMESTAMP_REPLY
17
ADDRESS_MASK_REQUEST
18
ADDRESS_MASK_REPLY
Table 52 Legal NetBIOS Commands
MESSAGE:
REQUEST:
POSITIVE:
VE:
RETARGET:
KEEPALIVE:
