The verify action, Table 4-8: procedures called during verify, The read action – Achronix Bitporter User Manual
Page 35: Table 4-9: procedures called during read
Using the Achronix STAPL Player
Picking a STAPL Action (-a option)
Bitporter User Guide
PAGE 29
The VERIFY Action
The VERIFY action verifies that the design contained in the STAPL file is the same design
found in the target device, with results reported to the command‐line. The VERIFY action may
be run/played when the device is in user mode, or when out of user mode. By default, only
core configuration memory is verified, excluding block RAM.
This Action will fail with error messages when run from files containing encrypted bitstreams.
(It is impossible for this action to succeed with encrypted bitstreams, since encrypted
bitstreams force the device into Secure Mode, and devices in Secure Mode disallow the
reading of configuration data.)
Note:
Verification of I/O ring configuration memory is not supported at this time.
Note:
The VERIFY and READ actions run slowly via JTAG on large modern FPGAs. Before
attempting these actions, please consult with Achronix Technical Support to discuss alternative
solutions and/or available optimizations.
The READ Action
The READ action reads the entire contents of the core configuration memory (optionally
including the block RAM contents) and dumps the contents to the console.
This action will log warnings when run from files containing encrypted bitstreams. (If the
device being read from is in Secure Mode, the results returned by this action are invalid.)
Note:
Reading the I/O ring configuration memory is not supported at this time.
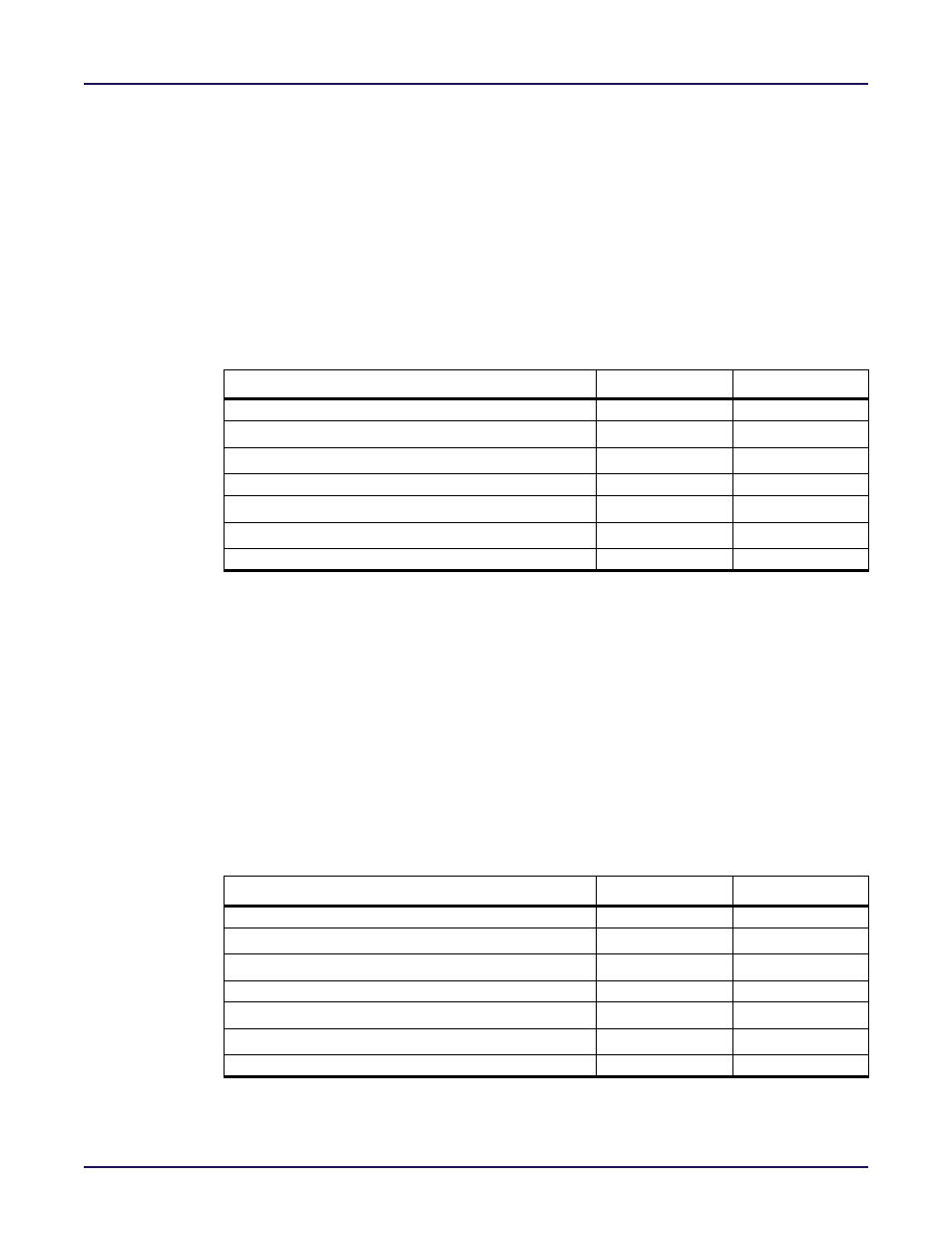
Table 4-8: Procedures Called During VERIFY
Procedure Name
Optional
Recommended
DO_ENTER_JTAG
DO_EXIT_USER_MODE
DO_BRAM_VERIFY
DO_VERIFY
DO_ENTER_USER_MODE
DO_EXIT_USER_MODE
DO_EXIT_JTAG
Table 4-9: Procedures Called During READ
Procedure Name
Optional
Recommended
DO_ENTER_JTAG
DO_EXIT_USER_MODE
DO_BRAM_READ
DO_READ
DO_ENTER_USER_MODE
DO_EXIT_USER_MODE
DO_EXIT_JTAG
