Vpn site-to-site sample configuration, Vpn site-to-site sample configuration -27, Central site branch sites – Enterasys Networks XSR-3150 User Manual
Page 71
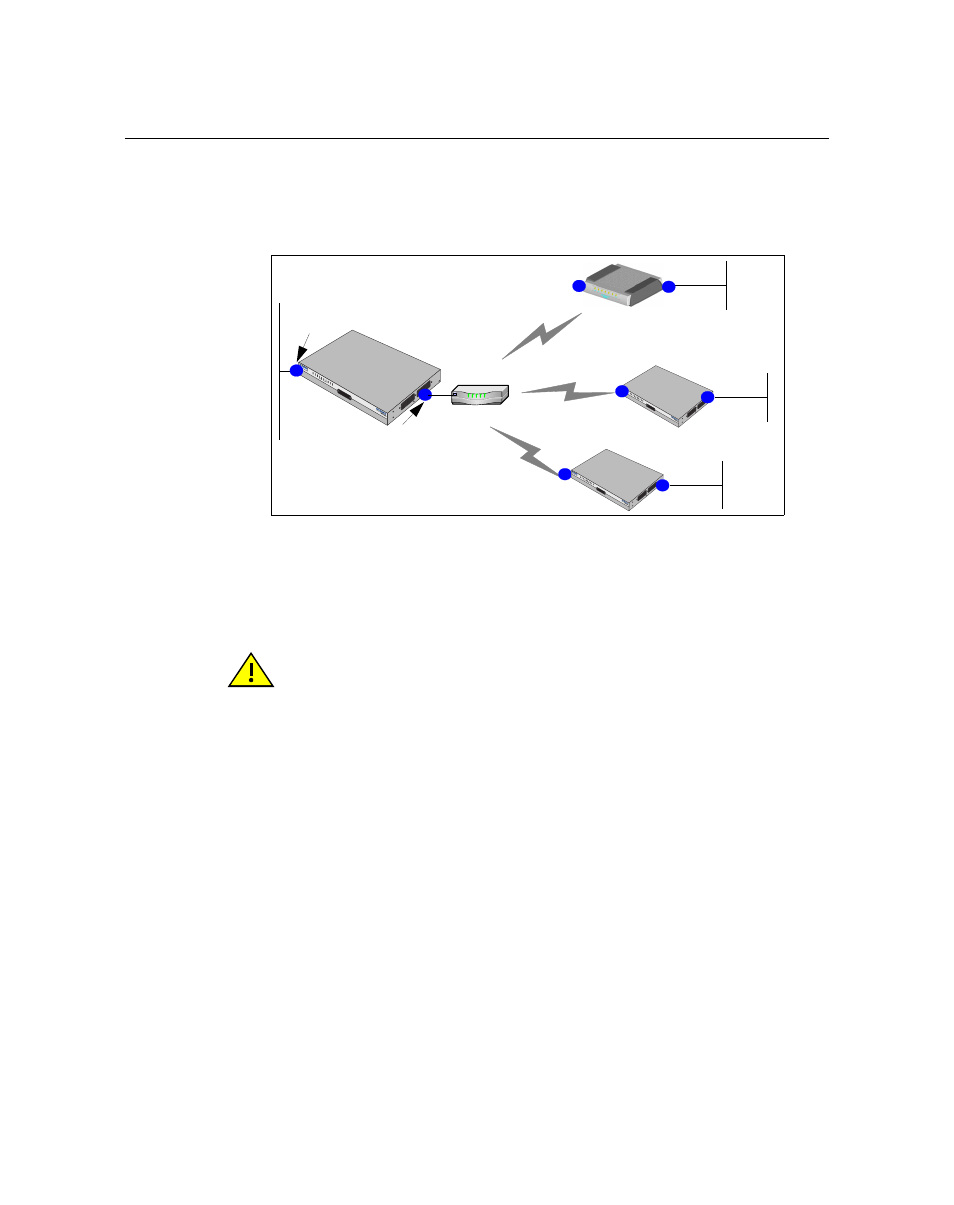
VPN Site-to-Site Sample Configuration
XSR Getting Started Guide 3-27
VPN Site-to-Site Sample Configuration
The following VPN topology, shown in
, configures a central site XSR to connect over
IPSec tunnels with a remote ANG-1105 and two XSRs.
Figure 3-5 VPN Site-to-Site Topology
The following script configures the VPN topology shown in
Generate Master Encryption Key
If you have not already generated a master encryption key, you must do so now to configure th6e
VPN. A master key need only be generated once.
Generate the master key:
XSR(config)#crypto key master generate
New key is 2173 4521 3764 2ff5
163b 4bdf fe92 dbc1
1232 ffe0 f8d9 3649
Configure Access Control Lists
ACL 101 configured below is strongly restrictive in denying all but IKE traffic (well-known UDP
port# 500) through the router. ACLs 190, 191, and 192 are crypto map filters configured to accept
any IPSec-encrypted traffic over site-to-site tunnels and pass that traffic to the three specified
networks only.
XSR(config)#access-list 101 permit udp any any eq 500
XSR(config)#access-list 101 permit udp esp any any
SEC
URIT
Y RO
UTE
RS
XSR
-1850
ETH
ERN
ET
POR
T 1
ETH
ERN
ET
POR
T 2
SYS
VPN
CON
SOLE
NIM
1
NIM
2
10/10
0BT
10/10
0BT
ACT
ACT
POW
ER
112.16.244.10
112.16.1.221
Central Site
Branch Sites
XSR
ANG-1105
Firewall
112.16.244.9
112.16.76.2
112.16.80.2
Gateway IP address
for all remote sites
SEC
URIT
Y RO
UTE
RS
XSR
-1850
ETH
ERN
ET
POR
T 1
ETH
ERN
ET
PORT
2
SY
S
VPN
CONS
OLE
NIM
1
NIM
2
10/1
00BT
10/10
0BT
AC
T
AC
T
POW
ER
112.16.244.7
SEC
URIT
Y RO
UTE
RS
XSR
-1850
ETHERN
ET
POR
T 1
ETH
ER
NET
PO
RT
2
SYS
VPN
CON
SO
LE
NIM
1
NIM
2
10/10
0BT
10/100
BT
AC
T
ACT
POW
ER
ANG-1105
XSR
112.16.244.5
112.16.72.2
XSR
Caution: The master encryption key is stored in hardware, not Flash, and you cannot read the
key - only overwrite the old key by writing a new one. To ensure router security, it is critical not to
compromise the key. There are situations where you may want to keep the key, for example, to
save the user database off-line in order to later download it to the XSR. In order to encrypt the
user database, you need the same master key, indicating the key designation with the master key
specify command. Be aware that if the XSR is inoperable you may have to return to factory
defaults, which erases the master key forcing you to generate a new one.
