Figure 60 syn flood figure 61 smurf attack – ZyXEL Communications P-660H-Tx v2 User Manual
Page 115
Chapter 8 Firewalls
P-660H-Tx v2 User’s Guide
115
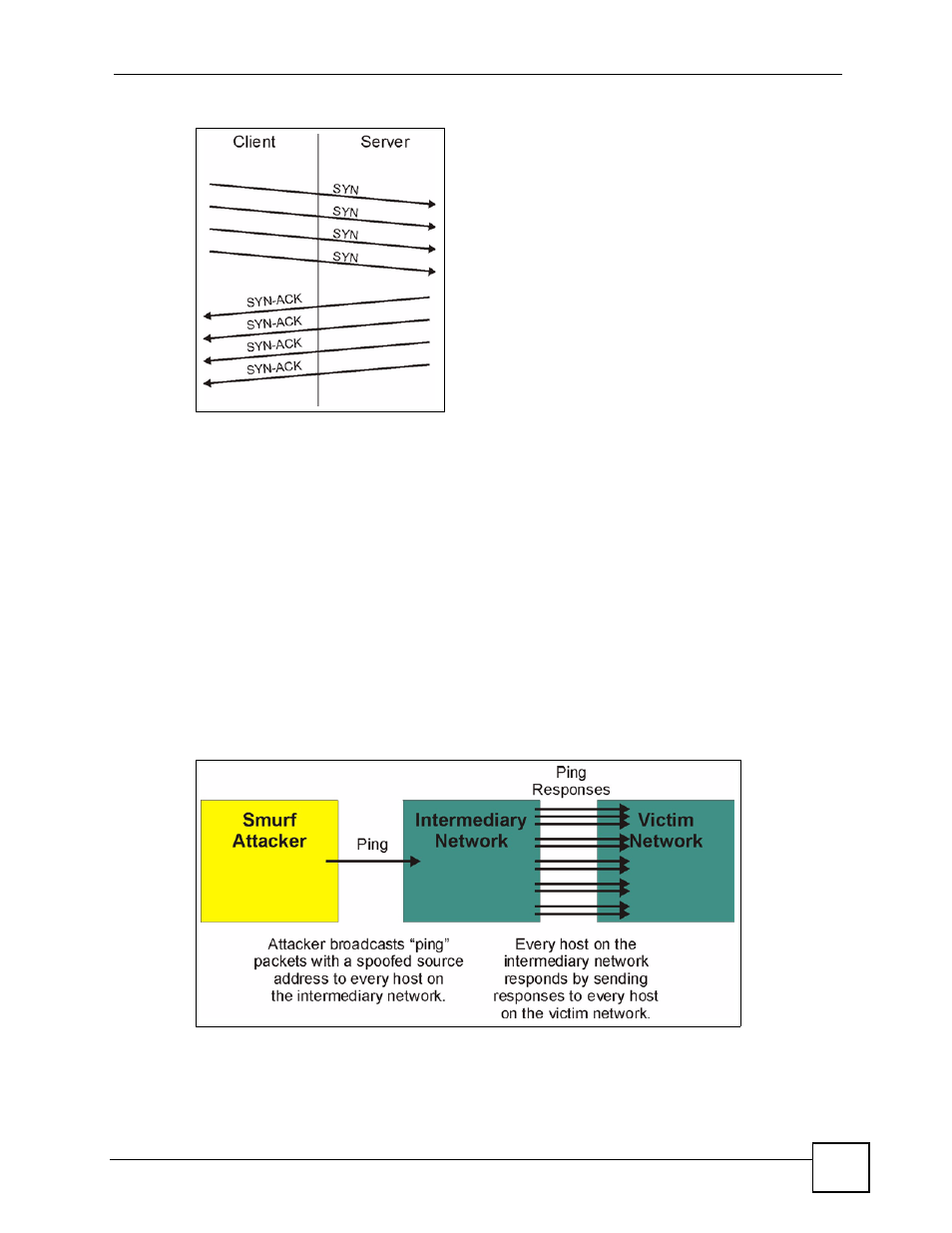
Figure 60 SYN Flood
• In a LAND Attack, hackers flood SYN packets into the network with a spoofed source IP
address of the targeted system. This makes it appear as if the host computer sent the
packets to itself, making the system unavailable while the target system tries to respond to
itself.
7 A brute-force attack, such as a "Smurf" attack, targets a feature in the IP specification
known as directed or subnet broadcasting, to quickly flood the target network with
useless data. A Smurf hacker floods a router with Internet Control Message Protocol
(ICMP) echo request packets (pings). Since the destination IP address of each packet is
the broadcast address of the network, the router will broadcast the ICMP echo request
packet to all hosts on the network. If there are numerous hosts, this will create a large
amount of ICMP echo request and response traffic. If a hacker chooses to spoof the
source IP address of the ICMP echo request packet, the resulting ICMP traffic will not
only clog up the "intermediary" network, but will also congest the network of the
spoofed source IP address, known as the "victim" network. This flood of broadcast
traffic consumes all available bandwidth, making communications impossible.
Figure 61 Smurf Attack
