Robustel R3000 Lite User Guide User Manual
Page 58
Robustel GoRugged R3000 Lite User Guide
RT_UG_R3000 Lite_v.1.0.0 23.12.2013 57 / 113
Confidential
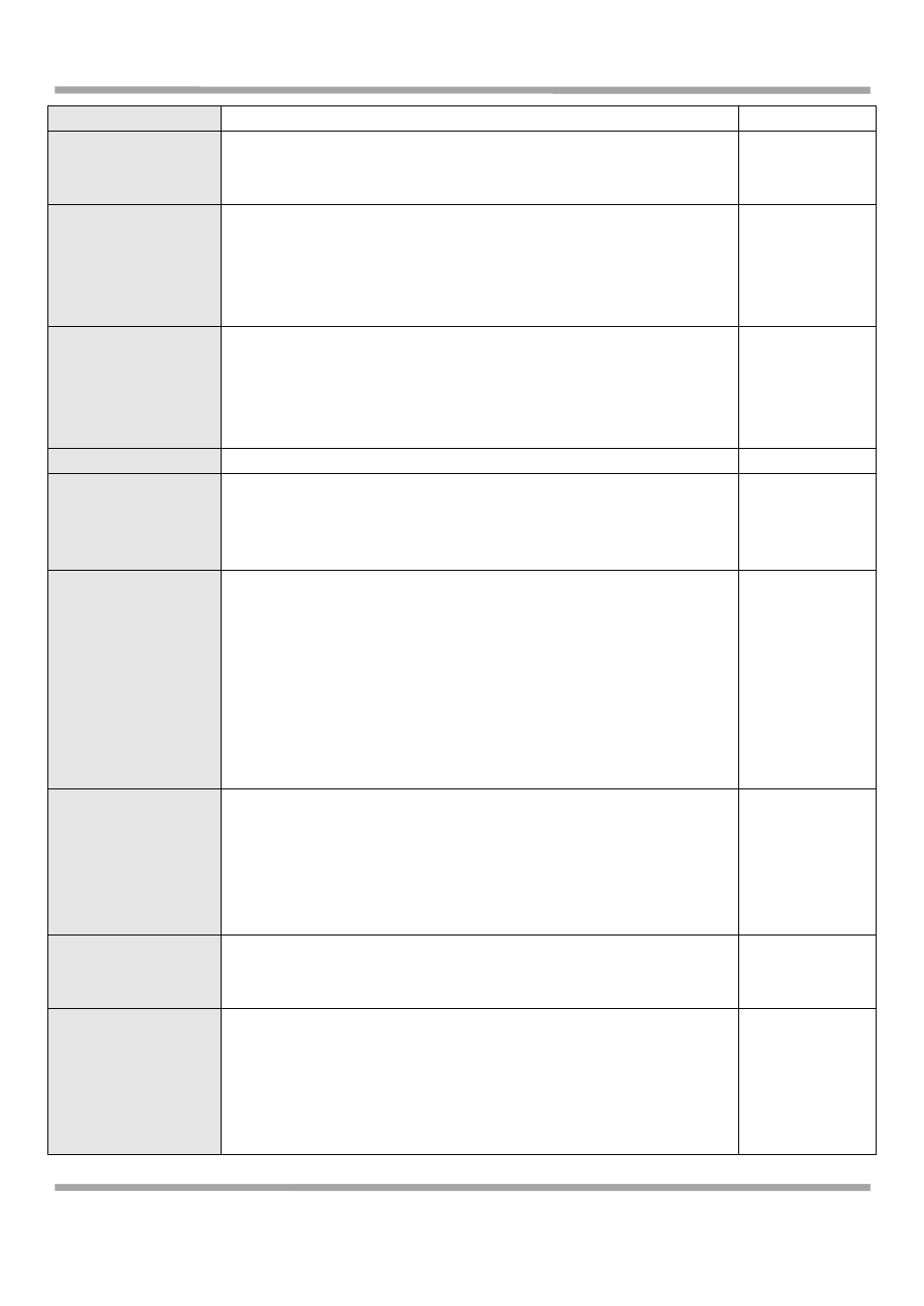
AES256: Uses the AES algorithm in CBC mode and 256-bit key.
Authentication
Algorithm
Select from “MD5” and “SHA1”to be used in IKE negotiation.
MD5: Uses HMAC-SHA1.
SHA1: Uses HMAC-MD5.
MD5
DH Group
Select from “MODP768_1”, “MODP1024_2” and “MODP1536_5”to be
used in key negotiation phase 1.
MODP768_1: Uses the 768-bit Diffie-Hellman group.
MODP1024_2: Uses the 1024-bit Diffie-Hellman group.
MODP1536_5: Uses the 1536-bit Diffie-Hellman group.
MODP1024_2
Authentication
Select from “PSK”, “CA”, “XAUTH Init PSK” and “XAUTH Init CA” to be
used in IKE negotiation.
PSK: Pre-shared Key.
CA: Certification Authority.
XAUTH: Extended Authentication to AAA server.
PSK
Secrets
Enter the Pre-shared Key.
Null
Life Time @ IKE
Parameter
Set the lifetime in IKE negotiation.
Before an SA expires, IKE negotiates a new SA. As soon as the new SA is
set up, it takes effect immediately and the old one will be cleared
automatically when it expires.
86400
SA Algorithm
Select from “DES_MD5_96”, “DES_SHA1_96”, “3DES_MD5_96”, “3DES_
SHA1_96”, “AES128_MD5_96”, “AES128_ SHA1_96”,
“AES192_MD5_96”, “AES192_ SHA1_96”, “AES256_MD5_96” and
“AES256_ SHA1_96” when you select “ESP” in “Protocol”;
Select from “AH_MD5_96” and “AH_ SHA1_96” when you select “AH”
in “Protocol”;
Note: Higher security means more complex implementation and lower
speed. DES is enough to meet general requirements. Use 3DES when
high confidentiality and security are required.
3DES_MD5_96
PFS Group
Select from “PFS_NULL”, “MODP768_1”, “MODP1024_2” and
“MODP1536_5”.
PFS_NULL: Disable PFS Group
MODP768_1: Uses the 768-bit Diffie-Hellman group.
MODP1024_2: Uses the 1024-bit Diffie-Hellman group.
MODP1536_5: Uses the 1536-bit Diffie-Hellman group.
PFS_NULL
Life Time @ SA
Parameter
Set the IPSec SA lifetime.
Note: When negotiating to set up IPSec SAs, IKE uses the smaller one
between the lifetime set locally and the lifetime proposed by the peer.
28800
DPD Time Interval
Set the interval after which DPD is triggered if no IPSec protected
packets is received from the peer.
DPD: Dead peer detection. DPD irregularly detects dead IKE peers.
When the local end sends an IPSec packet, DPD checks the time the last
IPSec packet was received from the peer. If the time exceeds the DPD
interval, it sends a DPD hello to the peer. If the local end receives no
180
