Operating notes for port security, Operating notes for port security -26 – SMC Networks SMC TigerStack II SMC6624M User Manual
Page 146
7-26
Using Passwords, Port Security, and Authorized IP Managers To Protect Against Unauthorized Access
Configuring and Monitoring Port Security
Usi
ng P
a
sswo
rds,
P
o
rt
Se
c
u
rity,
a
n
d
A
u
th
o
riz
e
d
IP
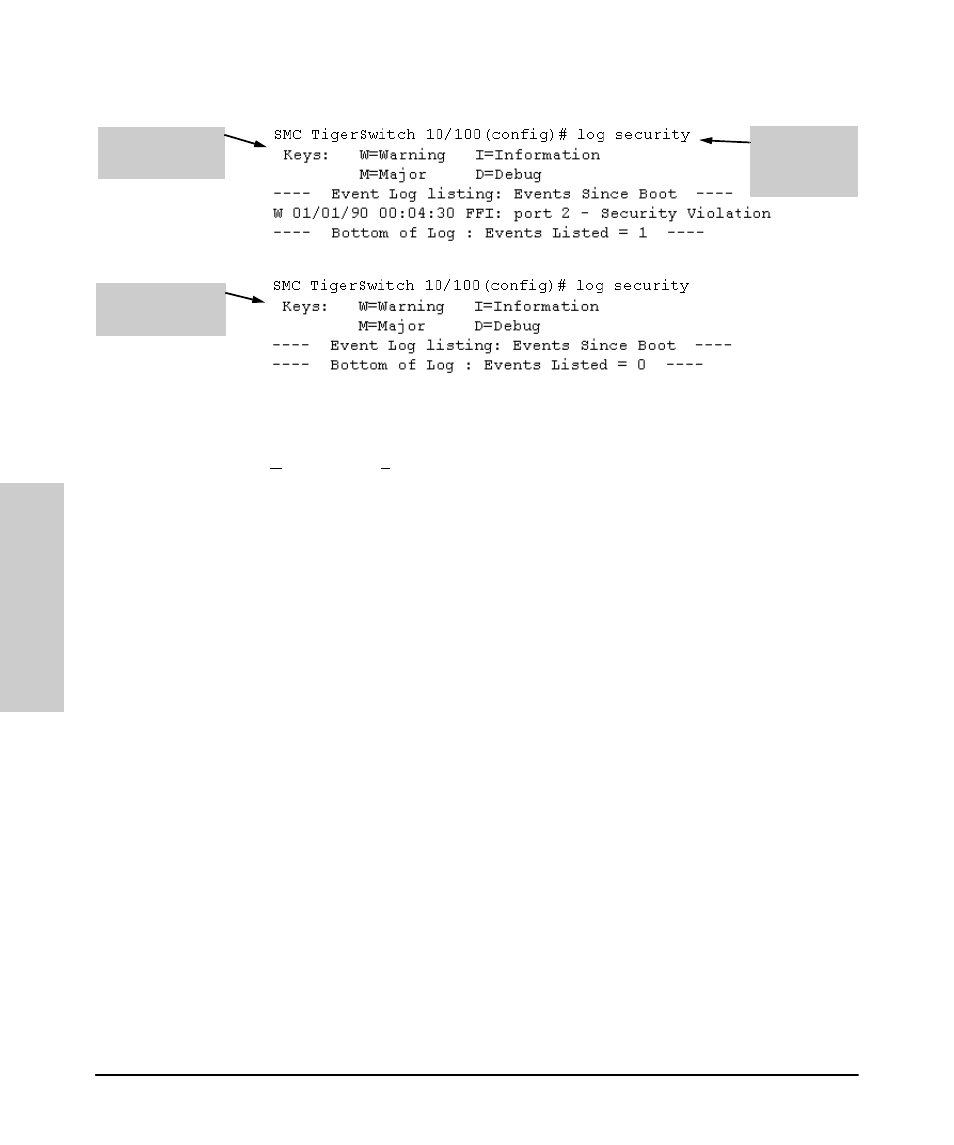
Figure 7-12. Example of Log Listing With and Without Detected Security Violation
From the Menu Interface:
In the Main Menu, click on
4. Event Log
and use
Next page and Prev page to review the Event Log contents.
For More Event Log Information.
See “Using the Event Log To Identify
Problem Sources” on page 11-10.
Web: Checking for Intrusions, Listing Intrusion Alerts, and
Resetting Alert Flags
1.
Check the Alert Log by clicking on the
Status tab and the [Overview]
button. If there is a “Security Violation” entry, do the following:
a.
Click on the
Security tab.
b.
Click on [Intrusion Log]. “Ports with Intrusion Flag” indicates any
ports for which the alert flag has not been cleared.
c.
To clear the current alert flags, click on [Reset Alert Flags].
Operating Notes for Port Security
Identifying the IP Address of an Intruder.
The Intrusion Log lists
detected intruders by MAC address. If you are using EliteView to manage your
network, you can use reports to link MAC addresses to their corresponding
IP addresses.
Proxy Web Servers.
If you are using the switch’s web browser interface
through a switch port configured for Static port security, and your browser
access is through a proxy web server, then it is necessary to do the following:
Log Listing with
Security Violation
Detected
Log Listing with No
Security Violation
Detected
Log Command
with
“security” for
Search String
