Firewall policy authentication – Fortinet FortiGate v3.0 MR7 User Manual
Page 48
FortiOS v3.0 MR7 User Authentication User Guide
48
01-30007-0347-20080828
Firewall policy authentication
Configuring authenticated access
When user authentication is enabled on a firewall policy, the authentication
challenge is normally issued for any of the four protocols (dependent on the
connection protocol). By making selections in the Protocol Support list, the user
controls which protocols support the authentication challenge. The user must
connect with a supported protocol first so they can subsequently connect with
other protocols. If you have selected HTTP, FTP, or Telnet, user name and
password-based authentication occurs: the FortiGate unit prompts network users
to input their firewall user name and password. If you have selected HTTPS,
certificate-based authentication (HTTPS, or HTTP redirected to HTTPS only)
occurs: you must install customized certificates on the FortiGate unit and on the
browsers of network users.
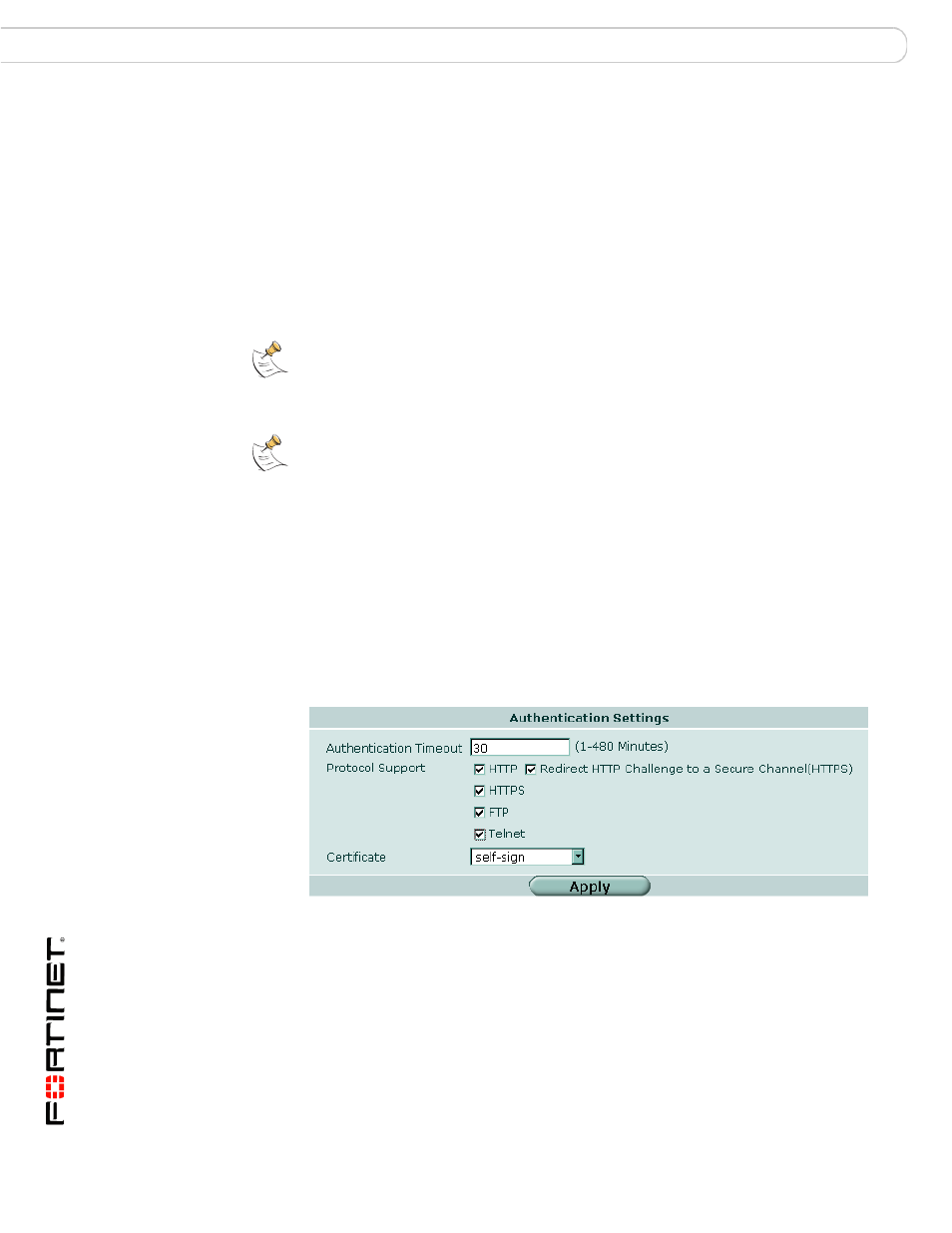
To set the authentication protocols
1
Go to User > Authentication.
2
In Protocol Support, select the required authentication protocols.
3
If using HTTPS protocol support, in Certificate, select a Local certificate from the
drop-down list.
4
Click Apply.
Figure 22: Authentication Settings
Firewall policy authentication
Firewall policies control traffic between FortiGate interfaces, both physical
interfaces and VLAN subinterfaces. Without authentication, a firewall policy
enables access from one network to another for all users on the source network.
Authentication enables you to allow access only for users who are members of
selected user groups.
Note: If you do not install certificates on the network user’s web browser, the network users
may see an SSL certificate warning message and have to manually accept the default
FortiGate certificate. The network user’s web browser may deem the default certificate as
invalid.
Note: When you use certificate authentication, if you do not specify any certificate when
you create the firewall policy, the global settings are used. If you specify a certificate, the
per-policy setting will overwrite the global setting. For information about the use of
certificate authentication,
rtiGate Certificate Management User Guide
.
