Collecting information configuring, Port information, General settings – Fortinet FortiDB-1000B User Manual
Page 2: Factory default settings
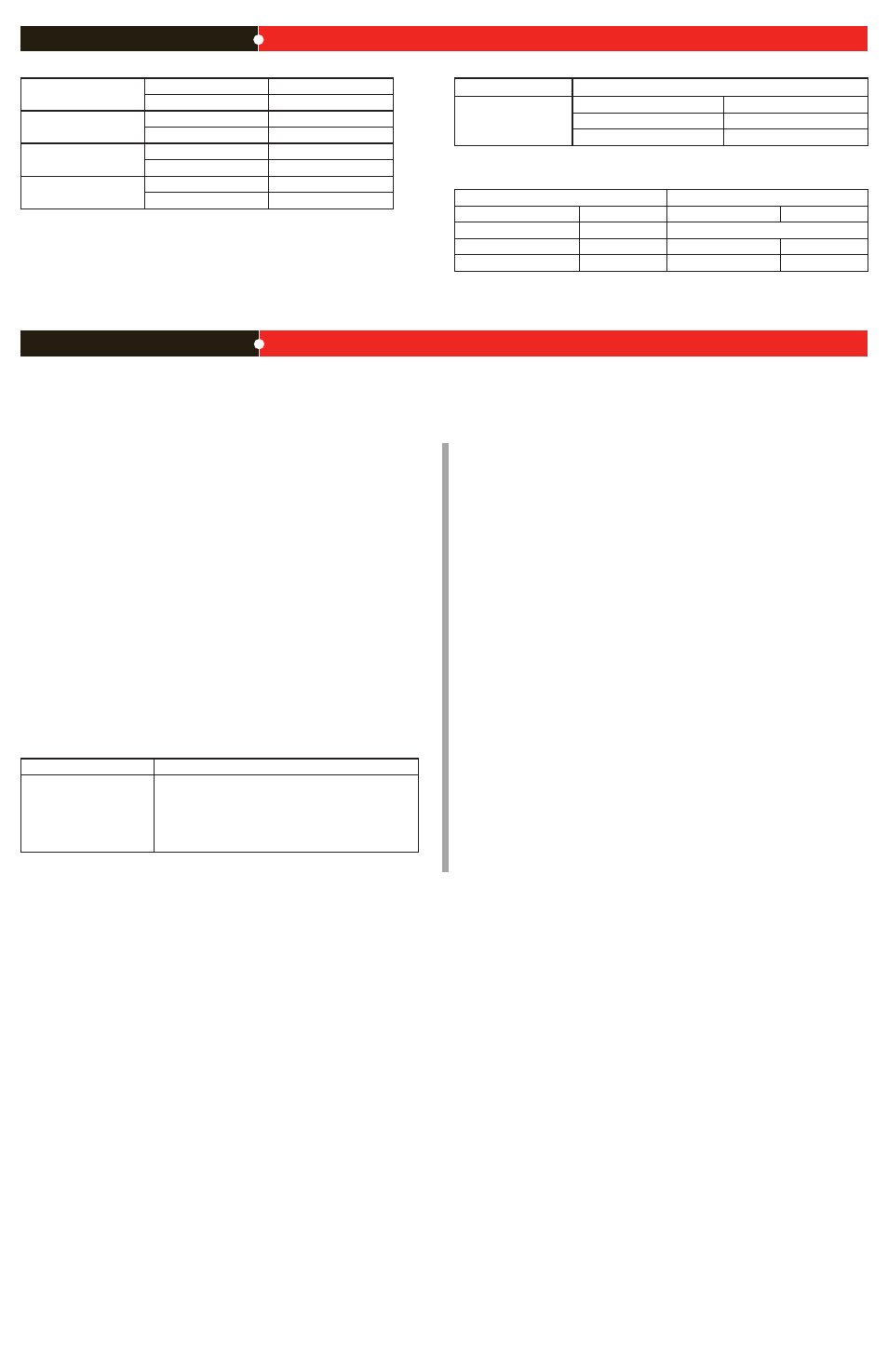
Port Information
Port 1
IP:
____.____.____.____
Netmask:
____.____.____.____
Port 2
IP:
____.____.____.____
Netmask:
____.____.____.____
Port 3
IP:
____.____.____.____
Netmask:
____.____.____.____
Port 4
IP:
____.____.____.____
Netmask:
____.____.____.____
The internal interface IP address and netmask must be valid for the internal network.
General settings
Administrator password:
Network Settings:
Default Gateway:
____.____.____.____
Primary DNS Server:
____.____.____.____
Secondary DNS Server:
____.____.____.____
Factory default settings
NAT/Route mode
Transparent mode
Port 1 interface
192.168.1.99
Management IP
0.0.0.0
Port 2 interface
0.0.0.0
Administrative account settings
Port 3 interface
0.0.0.0
User name
admin
Port 4 interface
0.0.0.0
Password
fortidb1!$
To reset the FortiDB unit to the factory defaults, in the CLI type the command
execute reset all-settings
Collecting Information
Configuring
Use the following CLI commands to configure the FortiDB unit for the network. For details on
using the CLI, see the CLI Reference.
Configuring the IP address and netmask
config system interface
edit port1
set ip
end
Configure the default gateway
config system route
edit 1
set device
set dst
set gateway
end
Application QuickStart
This section leads you through the process that results in the creation of a vulnerability
assessment report for one of your target databases.
Note: All GUI fields marked with an asterisk (*) must be filled in or specified.
Note: The example below assumes you will be assessing an Oracle target database.
Therefore you will need to make sure that the FortiDB user for your Oracle target database
has the privileges shown below. If your target is other than an Oracle one, refer to the
FortiDB Target Privilege Matrix in the FortiDB Administration Guide.
RDBMS
Required Privilege(s)
Oracle
CREATE SESSION
SELECT_CATALOG_ROLE
SELECT ON:
SYS.USER$
SYS.LINK$
SYSTEM.SQLPLUS_PRODUCT_PROFILE
•
•
•
•
•
•
Login to FortiDB as the FortiDB
admin user using fortidb1!$ for the password.
Create a FortiDB user who can create a target database group, run an assessment, and
review a report about that assessment.
Go to
Administration > User Management.
Select Add and select the General tab.
Enter the information in the text boxes marked with an asterisk (*). (Assume a user
name of
vauser and a password of fdb!23.)
On the Add New User page, select on the Roles tab.
Select these roles from the Available Roles list box:
Target Manager
Assessment Manager
Report Manager
Select the Right arrow button to move those role names to the Assigned Roles text
box.
Select Save.
Select Logout at the top-right of the screen to logout the admin user.
As the newly created user, create a target-database connection.
Login to FortiDB as the FortiDB
vauser user using fdb!23 for the password. You
should notice the absence of an Administration section in the left-side navigation
menu. (
vauser cannot create, or even view, other users from within the FortiDB
application.)
Go to
Target Management > Targets.
Select Add and select the General tab.
Enter the information in the text boxes marked with an asterisk (*) with settings
appropriate to your target database. Assume an Oracle target with these
parameters:
Name:
vatarget
Type:
Oracle
Port:
1521
Host Name:(IP address or machine name on your system that contains the
Oracle target database.)
User Name:(Name of the FortiDB user for your Oracle target database)
Password:(Password of the FortiDB user for your Oracle target database)
Select Test Connection to verify your target database is reachable and that your
connection parameters are correct. You should see a ‘Success’ message.
Select Save.
vatarget appears on the Targets page under the Alias Name column
1.
2.
a.
b.
c.
d.
e.
•
•
•
g.
h.
i.
3.
a.
b.
c.
d.
•
•
•
•
•
•
f.
g.
header.
Add the newly created connection to a target-database group.
Note: FortiDB runs assessments against target-database groups not individual data-
base connections. And a group can consist of one or more target database.
Go to
Target Management > Target Groups.
Select Add.
Enter a name for your group in the Group Name text box. (Here assume the group
name is
mygroup.)
Build a filter by filling in the following:
In the Column dropdown list, choose Database Name.
In the Operator dropdown list, choose Contains.
In the Value text box, enter all or part of the Name of the target you created
above (For example, use
targ, a substring within the name, vatarget, that
you assigned above.)
Select Apply to see if this filter selects the target you created above.
Select the Save icon.
Verify that the target group you just created is then listed on the Target Groups page.
Assess the vulnerability of the target database in your group.
Go to
Assessment Managment > Assessments.
Select Add.
Enter a name for your new assessment in the Assessment Name text box. (Here
assume the assessment name is
myscan.)
Associate your newly created target-database group with your assessment. Select
the Targets tab.
In the Available Target Groups list box in the Target Groups-tab, select
mygroup,
the target-database group you just created, and select the Right arrow button to
move
mygroup to the Assigned Target Groups text box.
Associate the appropriate group of FortiDB-shipped policies with your assessment.
Select the Policies tab.
In the Available Policy Groups list box in the Policy Groups tab, select Oracle Policy
Group (assuming you are assessing an Oracle target database) and then select
the Right Arrow button to move that group name to the Assigned Policy Groups text
box.
If you select a Policy Group in the Available Policy Groups or Assigned Policy
Groups list box, policies that belong to the Policy Group are displayed in the Active
Policies list box.
Note: The policies in the Active Policies lists box are selectable, but there is not
functionality in the selection.
Select Save. You should then see a ready-to-run assessment called myscan on the
Assessments page.
Run your newly created assessment. FortiDB offers assessment scheduling as well as
email and SNMP-trap notifications of assessment results. Here, however, we will simply
run the assessment created above which does not incorporate these features.
Select the checkbox to the left of the myscan row.
Select Run. After a minute, you should see the Last Run Time column in the
myscan row populated with a stop date and time for the assessment you just ran.
FortiDB ships with several pre-defined reports that will help you analyze your
assessments. Here we will examine our assessment with the Summary Failed Report
which summarizes failed-policy results.
Go to
Report Management > Pre-Defined Reports.
Select Summary Failed Report.
On the Vulnerability Assessment Summary Failed Report page, select:
myscan from the Assessment Name dropdown list
The start date and time associated with
myscan from the Assessment Time
dropdown list.
From the Target dropdown list, the target group (here
vatarget) associated
with
myscan On the Target Information tab of the Vulnerability Assessment
Summary Failed Report page, you will see the fields populated with the
parameters of your assessment.
Select the Preview Report tab of the Vulnerability Assessment Summary Failed
Report page and, after it is compiled, a Summary Failed Report appears in your
browser.
To view your report in another of the supported formats, scroll down to the Export
as drop down list, select a file format, and select Export. The following file formats
are supported:
Excel
Tab-delimited
Comma-separated values
4.
a.
b.
c.
d.
•
•
•
e.
5.
6.
a.
b.
c.
d.
e.
f.
g.
h.
7.
a.
b.
8.
a.
b.
c.
•
•
•
d.
e.
•
•
•
•
