Remedy for unauthorized operations – Konica Minolta bizhub PRESS C1060 User Manual
Page 31
bizhub PRESS C1070/C1070P/C1060, bizhub PRO C1060L
2-23
2.2
Administrator Security Functions
2
*1
: Audit log ID is saved as user ID when user authentication is successfully made, or when password incon-
formity occurs with a registered user name.
*2
: Audit log ID is saved as unregistered user ID when authentication failure occurs with an unregistered user
name.
The purpose of analyzing the audit log is to understand the following and implement countermeasures:
-
Whether or not data was accessed or tampered with
-
Subject of attack
-
Details of attack
-
Result of attack
For specific analysis methods, refer to the following description.
Specifying unauthorized actions: password authentication
If logs have NG as the result of password authentication (action: 01, 02, 11), items protected by passwords
may have been attacked.
-
Failed password authentication (NG) log entries specify who made the operation, and show if unauthor-
ized actions were made when password authentication failed.
-
Even if password authentication succeeded (OK), you may need to check whether a legitimate user cre-
ated the action. Careful check is recommended especially when successful authentication occurs after
series of failures, or for those made during times other than normal operating hours.
Specifying unauthorized actions: actions other than password authentica-
tion
Since all operation results other than password authentication are indicated as successful (OK), use ID and
action to determine if any unauthorized actions were made.
-
Check the time of operation, and see if the user who operated the specific subject made any unauthor-
ized actions.
Remedy for unauthorized operations
If you find that a password has leaked out after analyzing the audit log, change the password immediately.
-
The legitimate user may not be able to access the box because the password has been fraudulently
altered. The administrator must contact the user to confirm the situation, and if that is the case, he/she
must address the problem either by changing the password or by deleting the stored data.
-
If a stored document cannot be found or its content is altered, unauthorized actions may have been
occurred. If that is the case, similar countermeasures are needed.
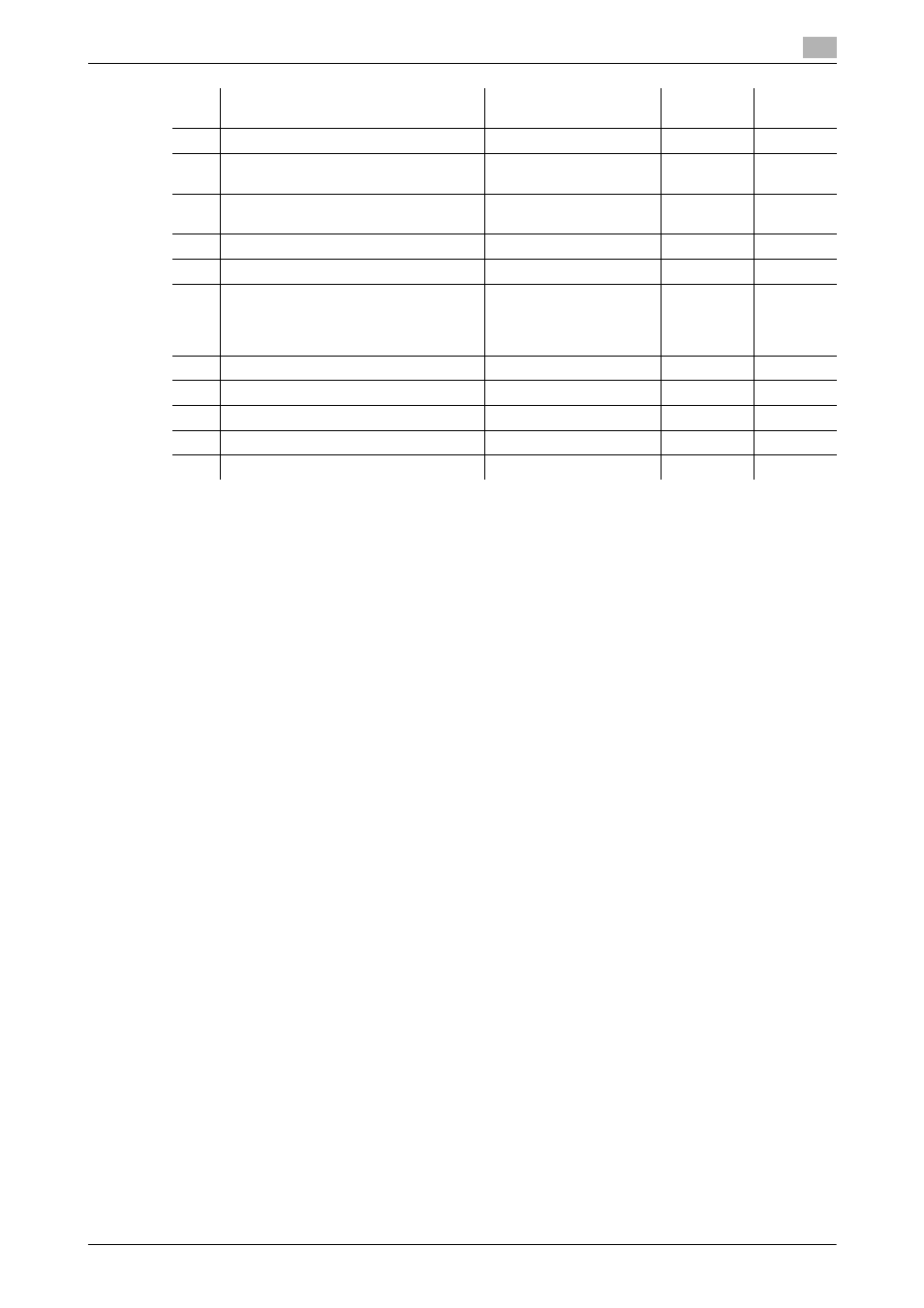
10
Change user attribute by administrator
User ID
10
OK
11
Password authentication for user
User ID
*1
/Unregistered
user ID
*2
11
OK/NG
12
Change attributes of user by user (user
password, etc.)
User ID
12
OK
13
(not used)
14
(not used)
15
Access to stored job
(Printing hold/HDD store job, recalling
HDD store job to hold job, storing hold
job on HDD)
User ID
15
OK
16
Delete store job
User ID
16
OK
17
(not used)
18
(not used)
19
Change HDD lock password
Administrator ID
19
OK
20
Date/Time setting
User ID
20
OK
No.
Operation
Audit ID
Stored ac-
tion
Result
