Data encryption with wpa-psk – Equinox Systems ZyAIR G-200 User Manual
Page 31
ZyAIR G-200 User’s Guide
Using the ZyAIR Utility
2-13
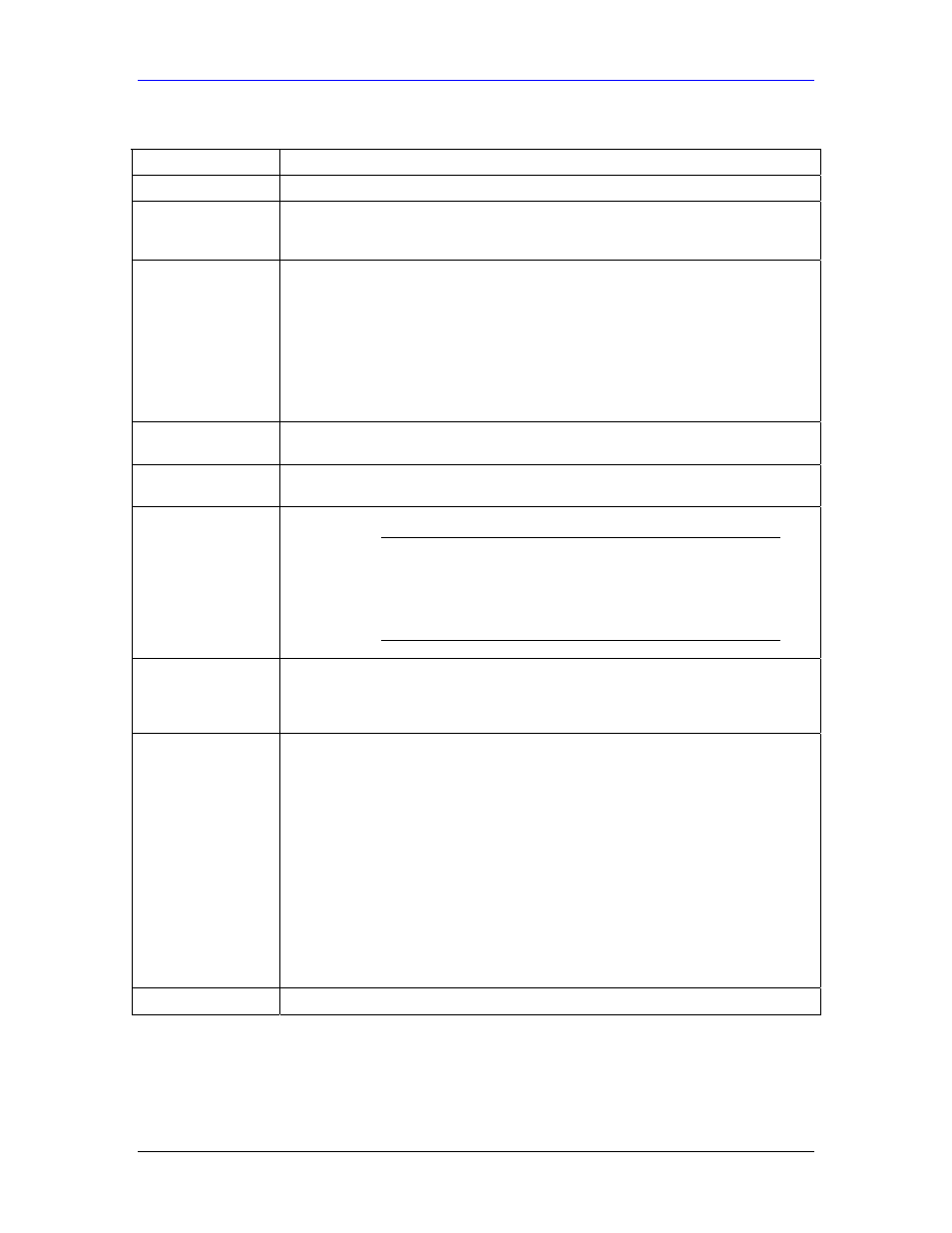
Table 2-5 WPA Authentication
FIELD DESCRIPTION
Authentication
Select WPA from the drop-down list box.
Encryption Status
All unicast traffic is automatically encrypted by TKIP when WPA or WPA-PSK
Authentication is selected. See the section on Encryption for details about
Temporal Key Integrity Protocol (TKIP).
EAP Type
Select an EAP Type from the drop-down list box. See Types of EAP Authentication
in the Appendix of this User’s Guide for information on the fields listed below. The
choices are:
EAP-TLS
EAP-TTLS
EAP-MD5
EAP-PEAP
LEAP
Login Name
If you want all wireless stations to have to enter user names before access to the
wired network is allowed, type a Login Name.
Password
If you want all wireless stations to have to enter passwords before access to the
wired network is allowed, type a Password.
Certificate
This field is only available when you select EAP-TLS in the EAP Type field.
You must first have a wired connection to
a network and obtain the certificate(s) from a
certificate authority (CA). Consult your
network administrator for more information.
Validate Server
Certificate
This field is not available when you select EAP-MD5 or LEAP from the EAP Type
list. The server presents a certificate to the client. After validating the identity of the
server, the client sends a different certificate to the server. Select the check box to
have your server validate this certificate.
TTLS Protocol/
PEAP Protocol
Select a protocol from the drop-down list box. The choices are:
EAP-TTLS
PAP
CHAP
MS CHAP
MS CHAP v2
EAP-PEAP
MD5 Challenge
EAP-GTC
MS CHAP v2
See the Types of EAP Authentication in the appendix for details.
OK
Click OK to apply the changes and close the screen.
2.6.3 Data Encryption with WPA-PSK
Select WPA-PSK from the Authentication drop-down list box to view the security configuration
options.
