Allowing inbound and outbound traffic, Disabling attack detection – 2Wire Gateway None User Manual
Page 60
Firewall Tab
55
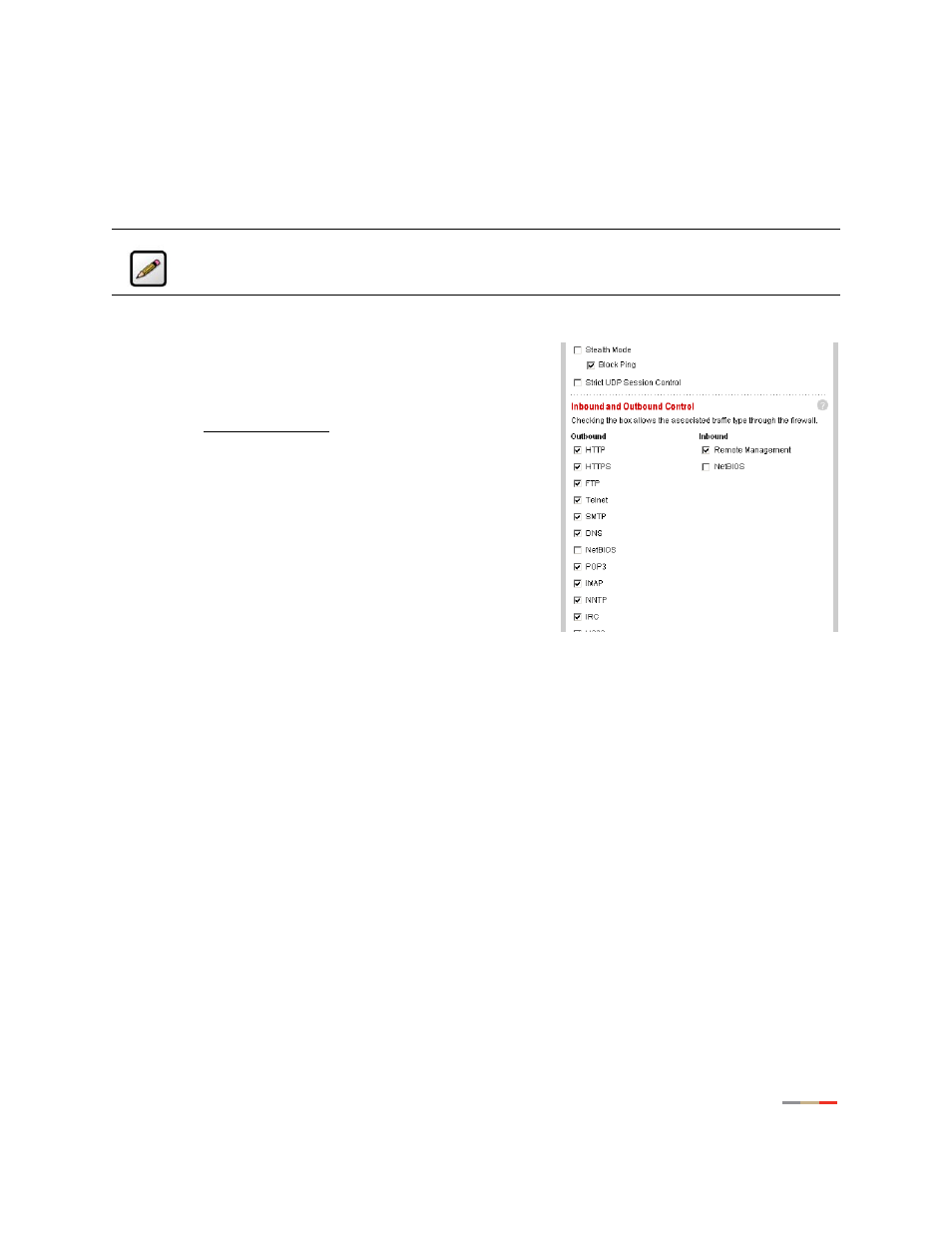
Allowing Inbound and Outbound Traffic
The Inbound and Outbound Control pane displays some common protocol types. When one of the Inbound
protocol boxes is checked, the firewall allows the corresponding protocol to pass through from the Internet
to the network. If one of the Outbound protocol boxes is checked, the firewall allows the traffic from the
network to pass through the firewall to the Internet.
To block an Inbound or Outbound protocol:
•
Open a Web browser and access the 2Wire gateway user
interface by entering http://gateway.2wire.net.
•
Click the
Firewall
tab.
•
Click the Advanced Settings link under the tab to open the
Edit Advanced Firewall Settings page.
1.
In the Inbound and Outbound Control pane, deselect the
checkbox of the protocol you wish to block.
2.
Click
SAVE
.
Disabling Attack Detection
By default, the 2Wire gateway firewall rules block the attack
types listed in the Attack Detection pane. There are some
applications and devices that require the use of specific data
ports through the firewall. The gateway allows users to open the necessary ports through the firewall using
the Firewall Settings page. If the user requires that a computer have all incoming traffic available to it, this
computer can be set to the DMZplus mode. While in DMZplus mode, the computer is still protected against
numerous broadband attacks (for example, SYN Flood or Invalid TCP flag attacks).
In rare cases, the incoming traffic may be inadvertently blocked by the firewall (for example, when
integrating with external third-party firewalls or VPN servers). You may need to disable one or more of the
attack detection capabilities for any device placed in the DMZplus. In this case, the third-party server
provides the attack protection normally provided by the gateway.
Note:
If you configure the firewall to block an Inbound protocol, you may disable support for
hosted applications that require that type of protocol.
